The Complete Malware Analyst Roadmap: Step-by-Step Guide
If you want to become a Malware Analyst, the biggest mistake is trying to jump
If you want to become a Malware Analyst, the biggest mistake is trying to jump
An in depth discussion with Uriel Kosayev on malware analysis, attacker mindset, EDR bypass techniques,
AI is not good or bad, it’s a mirror. It reflects how we use it.
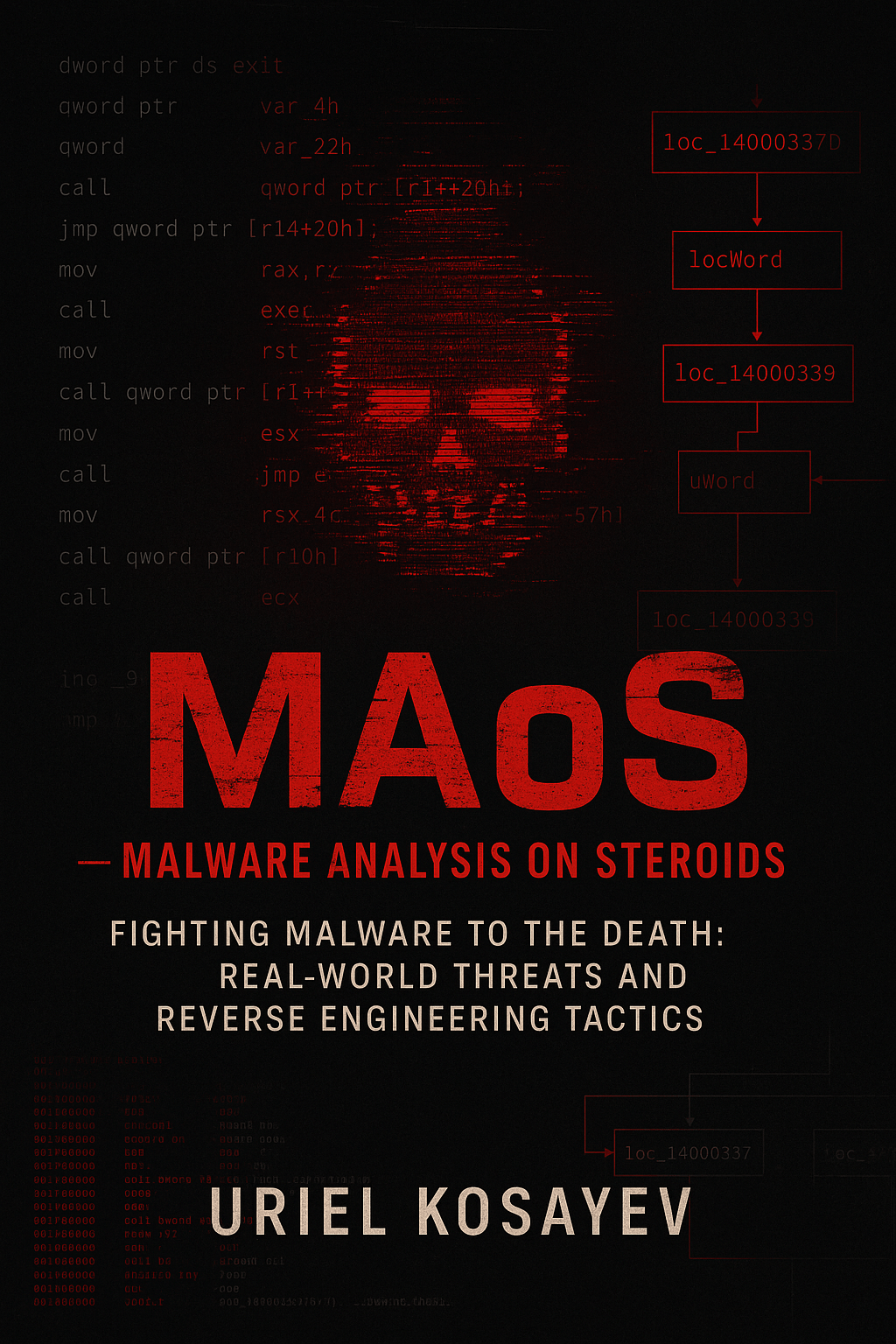
Unlike most malware books, this one doesn’t stay clean, academic, or theoretical. MAoS is a
This blog is not here to give you a “step-by-step recipe.” It’s here to open
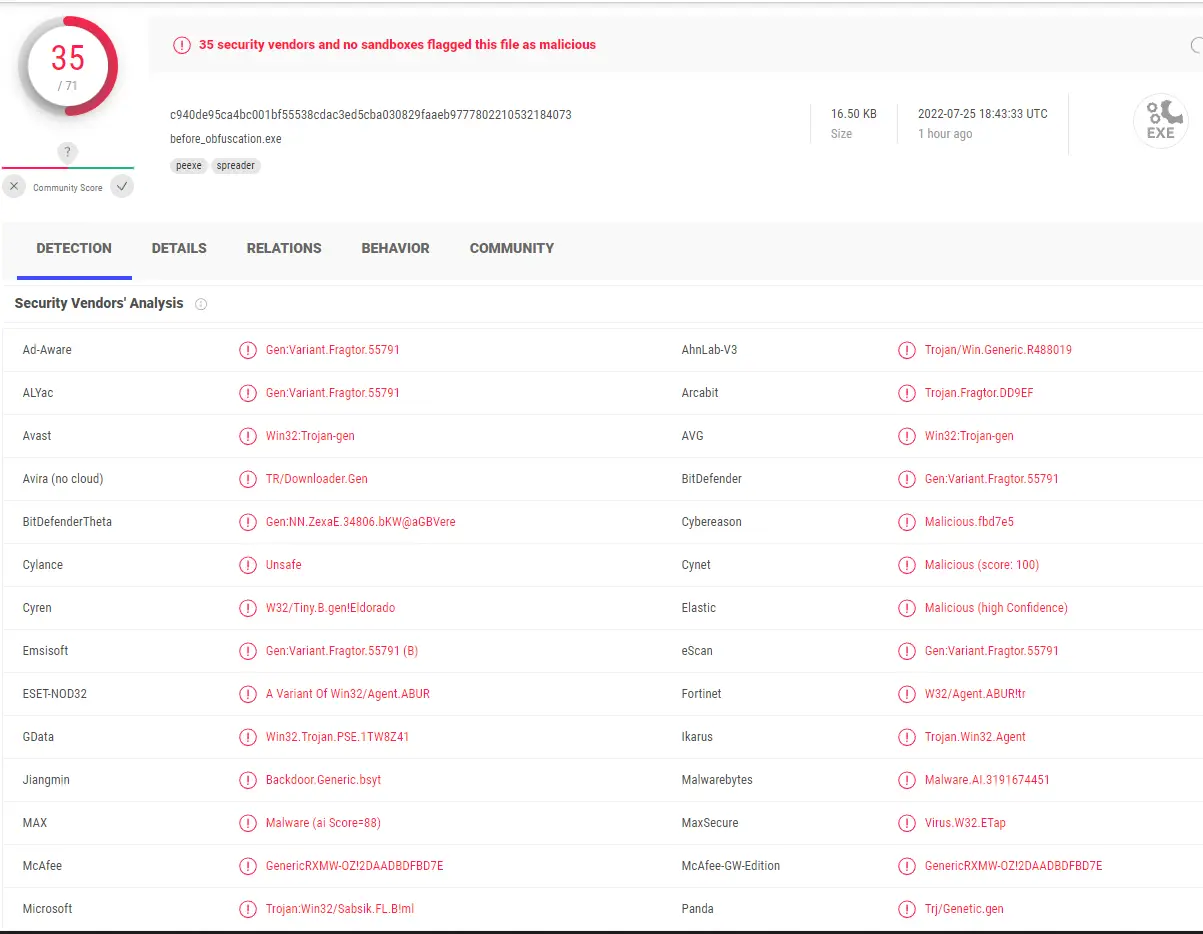
There are a variety of threats in today’s cyber landscape, but one of the biggest
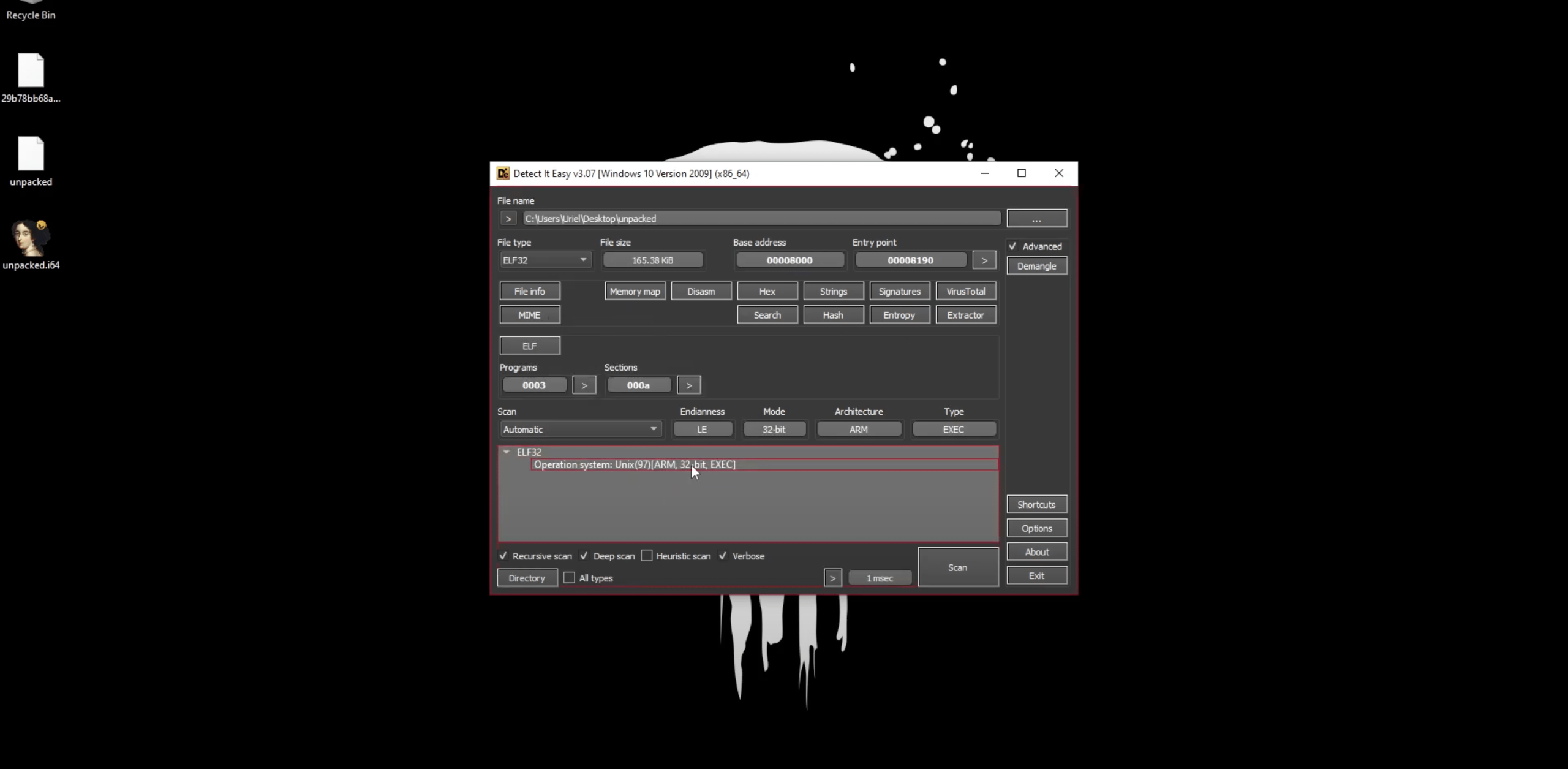
In this video, I’ll walk you through my methodology and insights gained when uncovering how
We’re excited to share the recorded workshop on Remote Thread Injection and EDR-based detection that
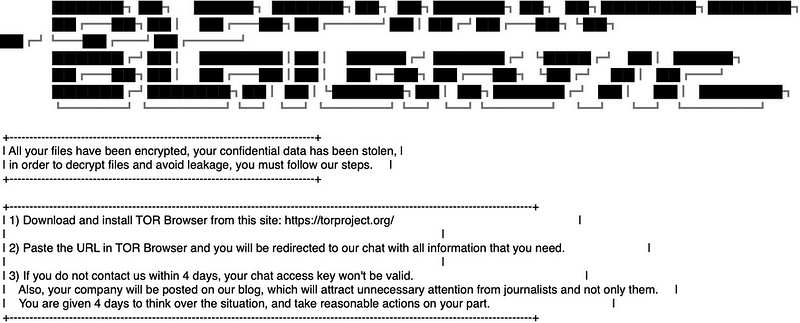
Explore BlackByte ransomware: ProxyShell exploits, anti-debugging, and reverse engineering insights. Dive deep into this malware’s
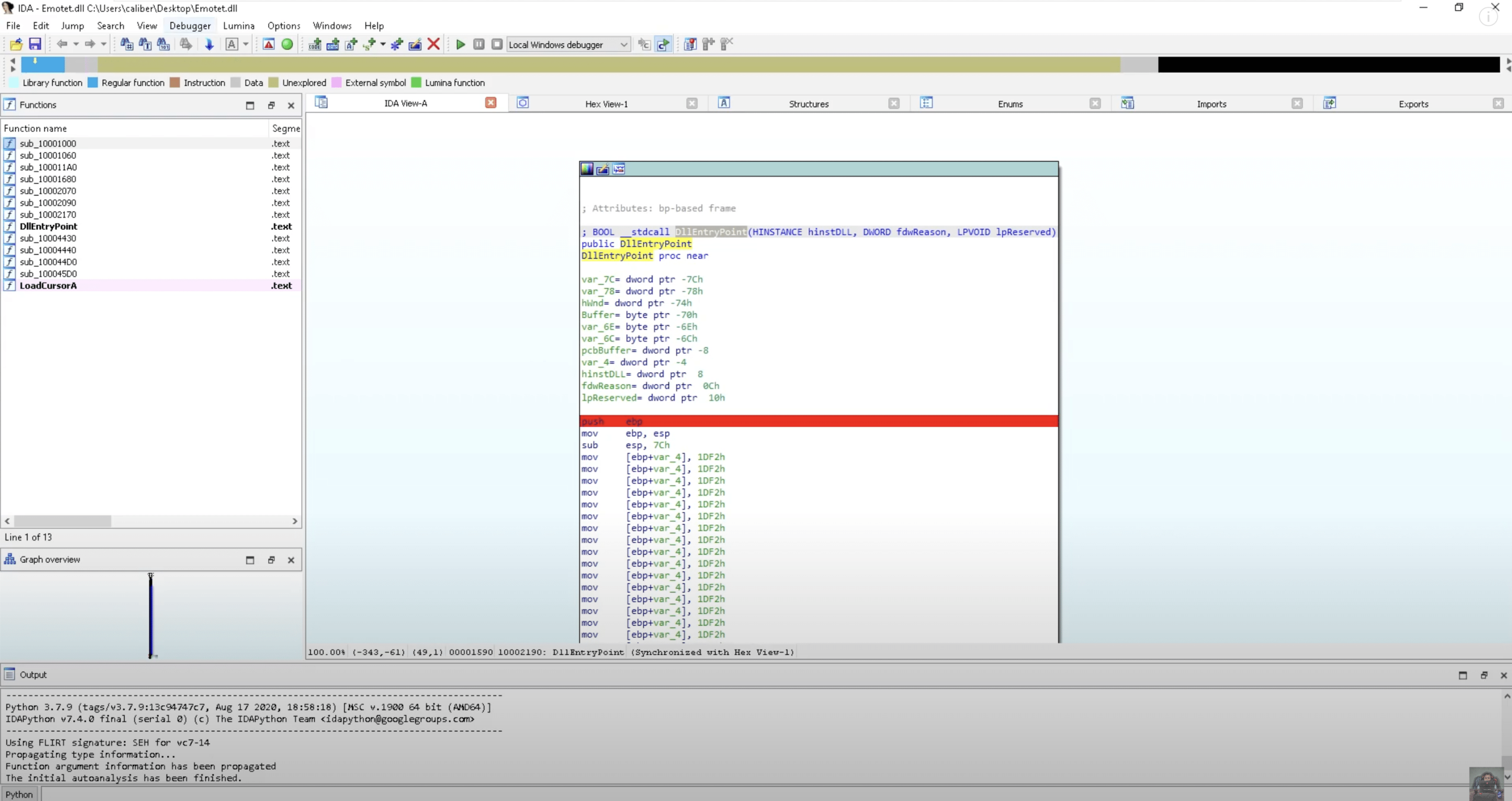
IDA (Interactive DisAssembler) is a professional reverse engineering tool used to analyze compiled software by