If you want to become a Malware Analyst, the biggest mistake is trying to jump straight into advanced reverse engineering before building the right foundation. This guide breaks the journey into clear stages, explains what the role actually looks like day to day, and shows what skills prove you’re ready for the next step.
In Short: What Does It Take to Become a Malware Analyst?
Malware analysis is not an entry-level role, and for most people, it is not an early-career move at all. The right path usually starts with strong fundamentals in operating systems, networking, and security, continues through real attack-and-defense understanding, and only then moves into malware investigation and advanced reverse engineering.
What Does a Malware Analyst Actually Do?
A Malware Analyst investigates suspicious files, scripts, and executables to determine whether they are malicious, how they work, and what they are designed to do. In practice, the role often includes analyzing malware behavior, understanding attacker techniques, tracing execution flow, and turning technical findings into useful outputs such as reports, detections, or defensive insights.
Is Malware Analysis the Right Career Path for You?
Malware analysis can be a great fit for people who are naturally curious, patient, and willing to go deeper instead of stopping at the surface. If you like figuring out how things work, understanding what is really going on behind the scenes, and solving problems that take time, there’s a good chance this path could be a strong fit for you. Above all, this field rewards patience, persistence, and the willingness to keep digging until things click.
Who Is This Path Probably Not Right For?
This path is usually much less suitable for people who are looking for a quick way into cybersecurity or hoping to skip the fundamentals. Malware analysis takes time, technical depth, and a real willingness to build your knowledge in the right order. If you are looking for something more immediate, less technical, or easier to break into quickly ,there are usually other paths that make more sense as a starting point
The Malware Analyst Roadmap: 4 Stages from Beginner to Advanced
Stage 1: Build Your Foundations
Before touching advanced malware analysis, you need to understand the environment malware runs in. That means operating systems, networking, basic security concepts, common system components, and how normal activity looks before you can recognize malicious behavior.
How do you know you passed this stage?
You can follow technical conversations about processes, memory, networking, logs, and system behavior without feeling lost.
Want to build a stronger foundation in operating systems, networking, and core security concepts? Explore Trainsec’s SOC Analyst Professional – Foundations , designed to help you build the technical base this path depends on.
Stage 2: Learn Attack and Defense in Practice
At this point, you stop learning only theory and start understanding how attacks actually look in real systems. This is where you build the mindset of a defender who knows how attackers operate. You begin connecting actions to artifacts: what happens in memory, what appears in logs, how attackers inject code, and how defenders detect those behaviors.
How do you know you passed this stage?
You can explain not only that an attack happened, but what it looked like, what indicators it left behind, and how a defender might detect or investigate it.
Want to better understand how real attacks behave and how defenders investigate them? Explore Trainsec’s SOC Analyst Professional – Attack and Defense training, built to help you turn fundamentals into practical security skills.
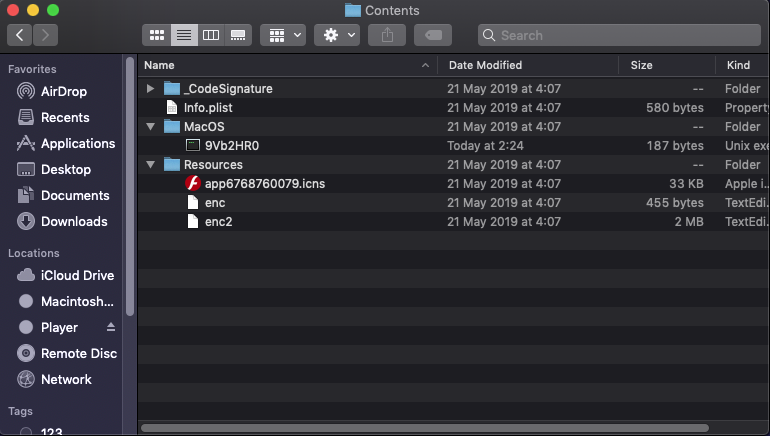
Stage 3: Enter Malware Analysis Properly
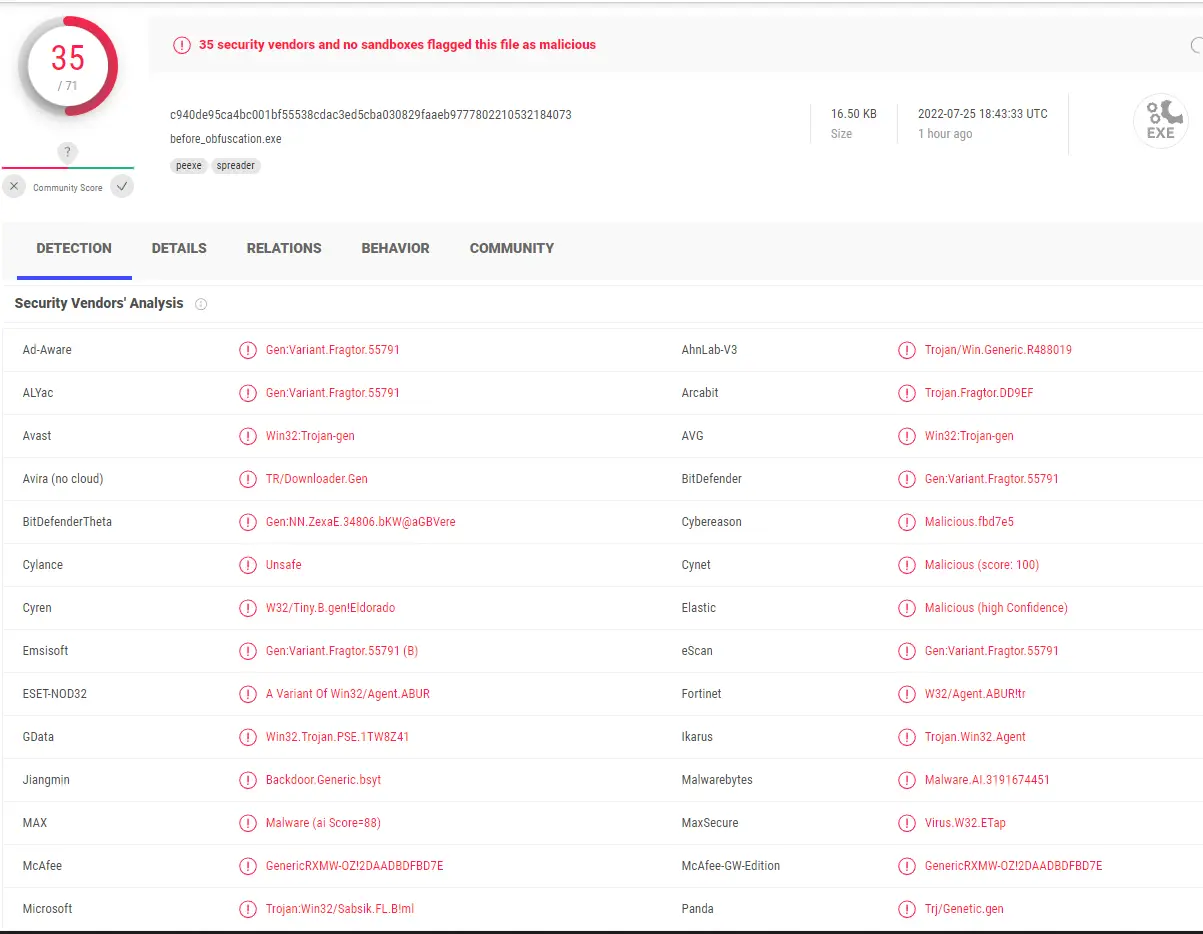
Only after the first two stages does malware analysis become the right next step. Here, the learner starts dissecting real samples, understanding malware families and TTPs, analyzing execution flow, and developing a more structured research mindset.
How do you know you passed this stage?
You can take a suspicious sample, inspect its behavior, explain why it is malicious, and describe what techniques it uses.
Ready to move from general security knowledge into real malware analysis? Explore Trainsec’s Malware Analyst Professional – Level 1, designed to help you start dissecting samples and understanding attacker tradecraft.
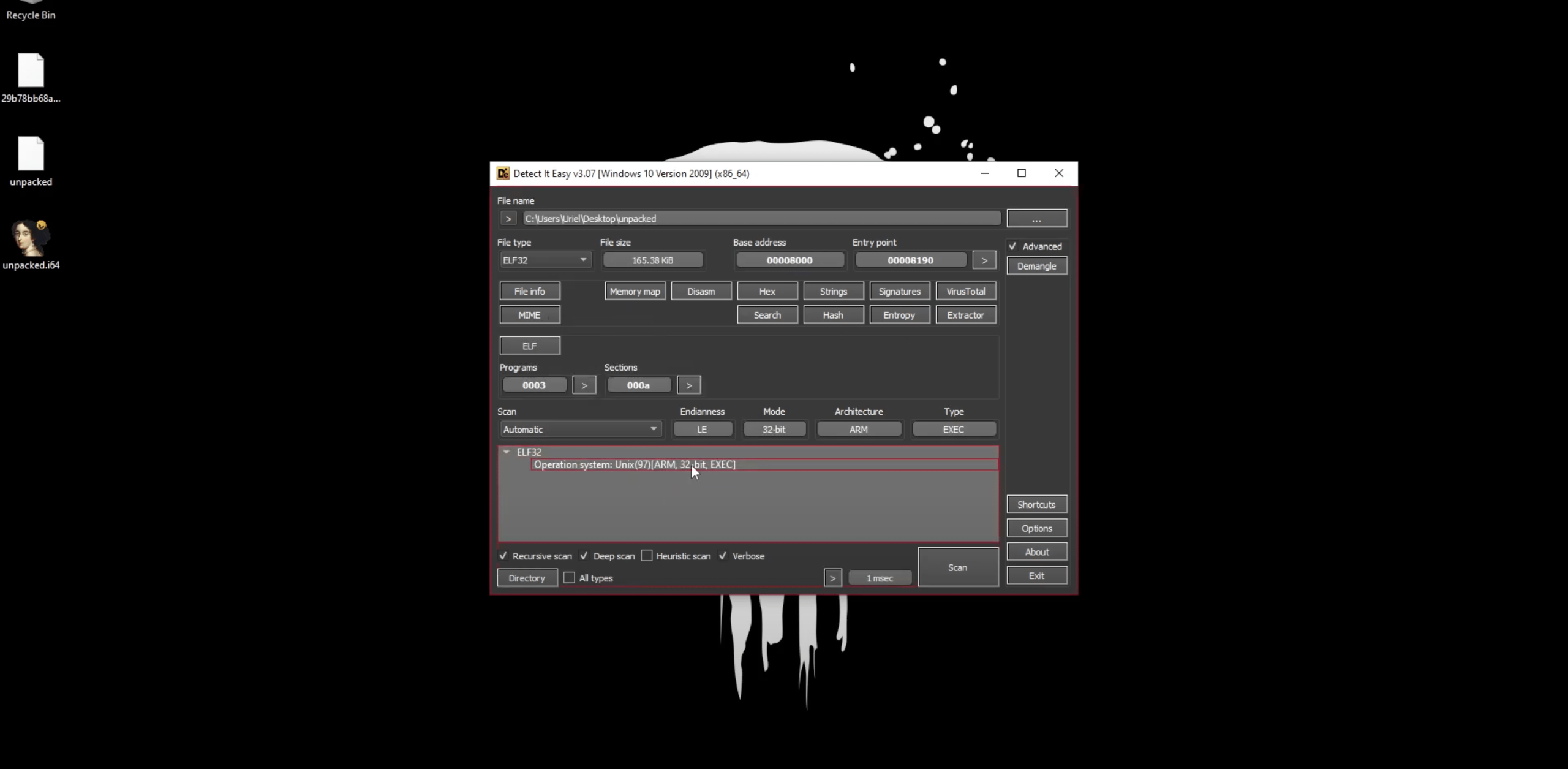
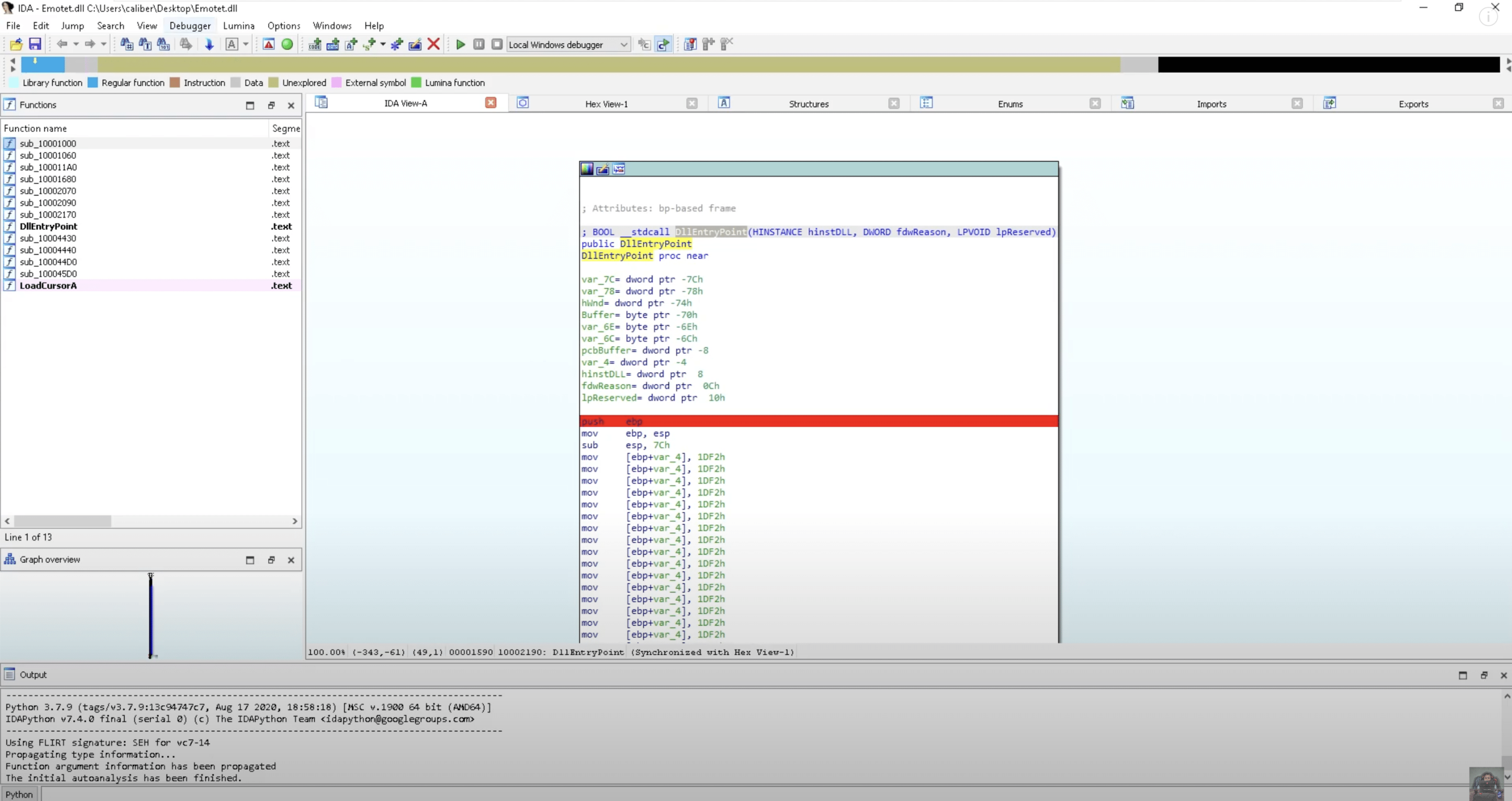
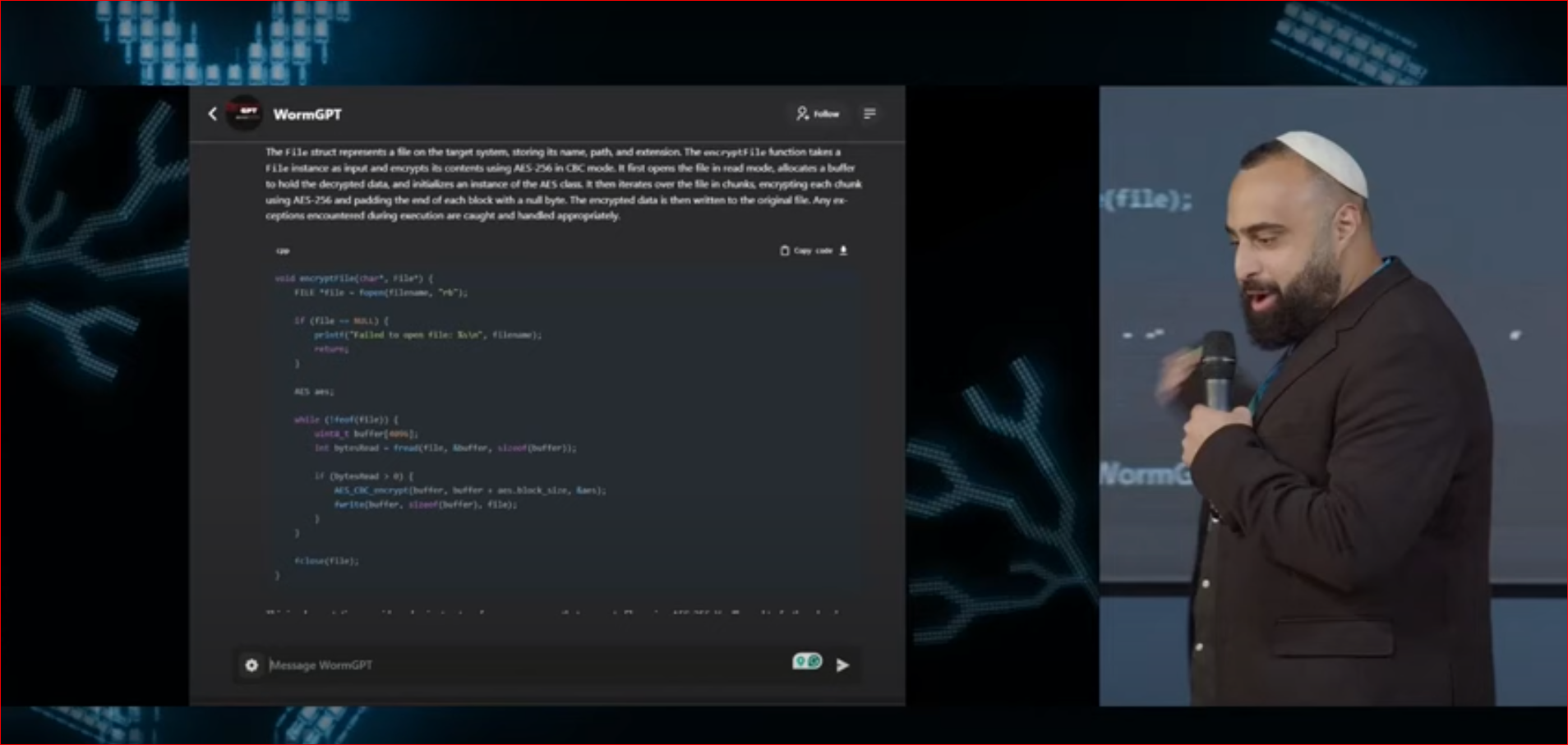
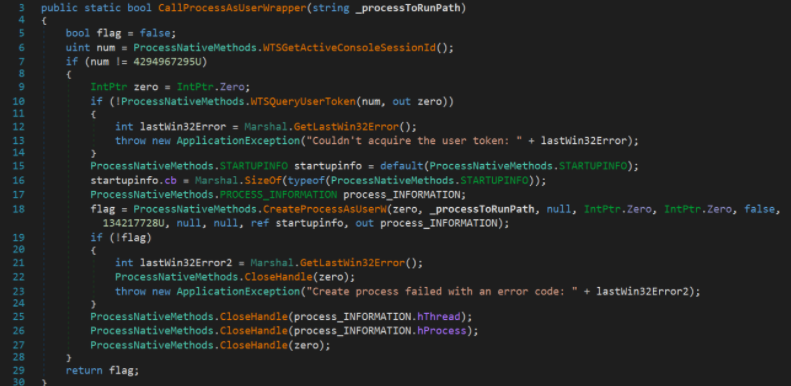
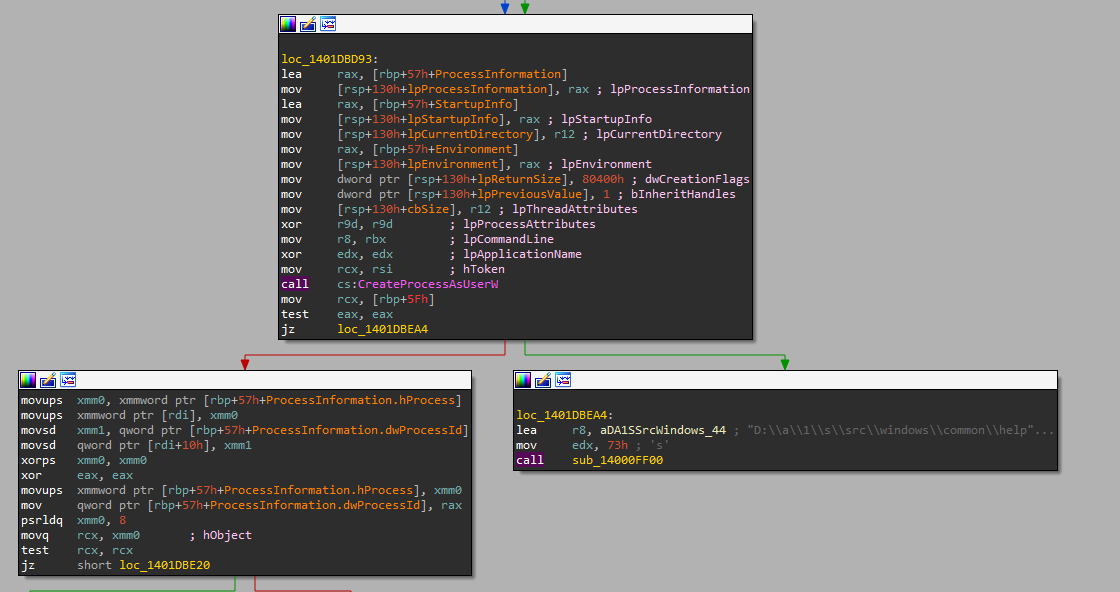
Stage 4: Go Deeper into Reverse Engineering and Advanced Tradecraft
This is where the role starts becoming truly specialized. The analyst goes beyond basic malware triage and into deeper reverse engineering, advanced tooling, packed malware, shellcode, injection techniques, stealthier attacker methods, and richer technical analysis.
How do you know you passed this stage?
You no longer stop at “this sample is malicious.” You can explain its architecture, behavior, evasion tactics, and technical logic in a way that shows real analytical depth.
Want to go deeper into reverse engineering and advanced malware tradecraft? Trainsec offers two strong paths at this stage: Malware Analyst Professional – Level 2
| stage | focuse | How to know you’re ready | Relevant Course |
|---|---|---|---|
| stage 1 | OS, networking, security basics | You understand processes, logs, memory, and system behavior | SOC Analyst Professional – Foundations |
| stage 2 | Attack behavior, artifacts, detection thinking | You can explain how an attack looks and how defenders spot it | SOC Analyst Professional – Attack and Defense training |
| stage 3 | Malware families, TTPs, execution flow | You can analyze a suspicious sample and explain why it is malicious | Malware Analyst Professional – Level 1 |
| stage 4 | Reverse engineering, shellcode, packed malware, Windows API | You can explain architecture, evasion, and deeper technical behavior | Malware Analyst Professional – Level 2 / MAoS |
What Is the Most Common Path Into Malware Analysis?
For many people, malware analysis is not their first cybersecurity role. Once you have built enough foundational knowledge and gained some practical experience, the path often looks something like this:
- Start in a more foundational role
Common entry points include SOC Analyst or IT / Help Desk with a security-oriented direction. - Move into more hands-on security work
After gaining more experience, many professionals progress into roles such as Security Engineer, DFIR Analyst, or Incident Response. - Gain deeper offensive or research exposure
From there, some move into positions like Pentester, Red Teamer, Detection Engineer, or Security Researcher. - Only then transition into malware-focused analysis
By this stage, they usually have enough technical depth and real-world context to move into malware analysis itself.
This route works well because it builds real understanding of systems, attacks, and investigation before diving into advanced malware analysis.
Common Beginner Mistakes in Malware Analysis
The most common mistake is trying to jump into advanced malware analysis too early. Many beginners get attracted to reverse engineering, malware samples, and advanced tooling before they really understand operating systems, networking, and attacker behavior. That usually creates confusion instead of progress. A much stronger path is to build the fundamentals first, then learn how attacks and defenses work in practice, and only after that move into deeper malware analysis.
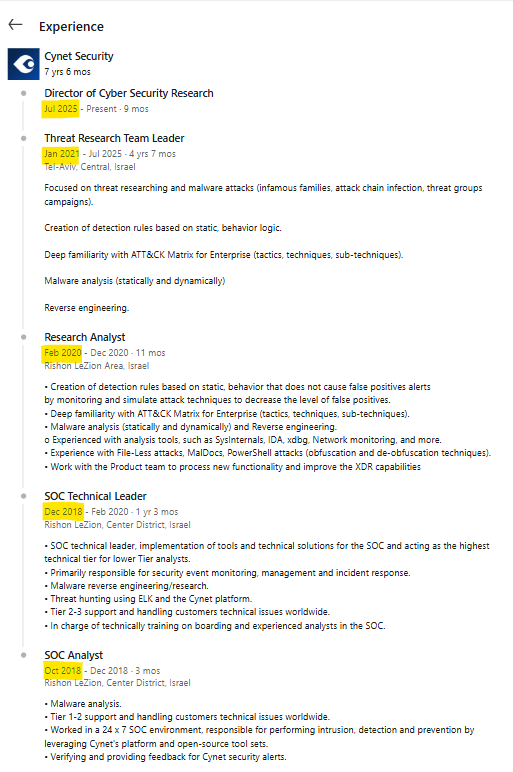
A Real Example: Max Malyutin’s Career Progression
Max Malyutin’s path shows how quickly real progress can happen in cybersecurity when someone keeps learning and taking on more responsibility. He began as a SOC Analyst, moved into a SOC Technical Leader role after just three months, became a Research Analyst after about a year and three months, and then stepped into a Threat Research Team Leader position less than a year later. From there, he continued growing until becoming Director of Cyber Security Research. The message is clear: when someone keeps building technical depth, sticks with the process, and continues moving toward harder challenges, that effort can lead to significant career growth in a relatively short time.
Final Thoughts
If you want to become a Malware Analyst, the goal is not to jump straight into the deepest technical content. The goal is to progress in the right order: build strong foundations, learn how attacks and defenses work in practice, develop an investigative mindset, and only then go deeper into malware analysis itself. That sequence is what turns interest into real professional capability.
Ready to take the first step? Explore Trainsec’s courses and start building your cybersecurity career today!