A lot of people are drawn to malware analysis because it sounds advanced, technical, and impressive. And it is. But before thinking about courses, job titles, or “how to get in” it is worth asking a simpler question first: who usually ends up being a good fit for this kind of work?
What Kind of Personality Fits This Path?
You like to understand how things really work
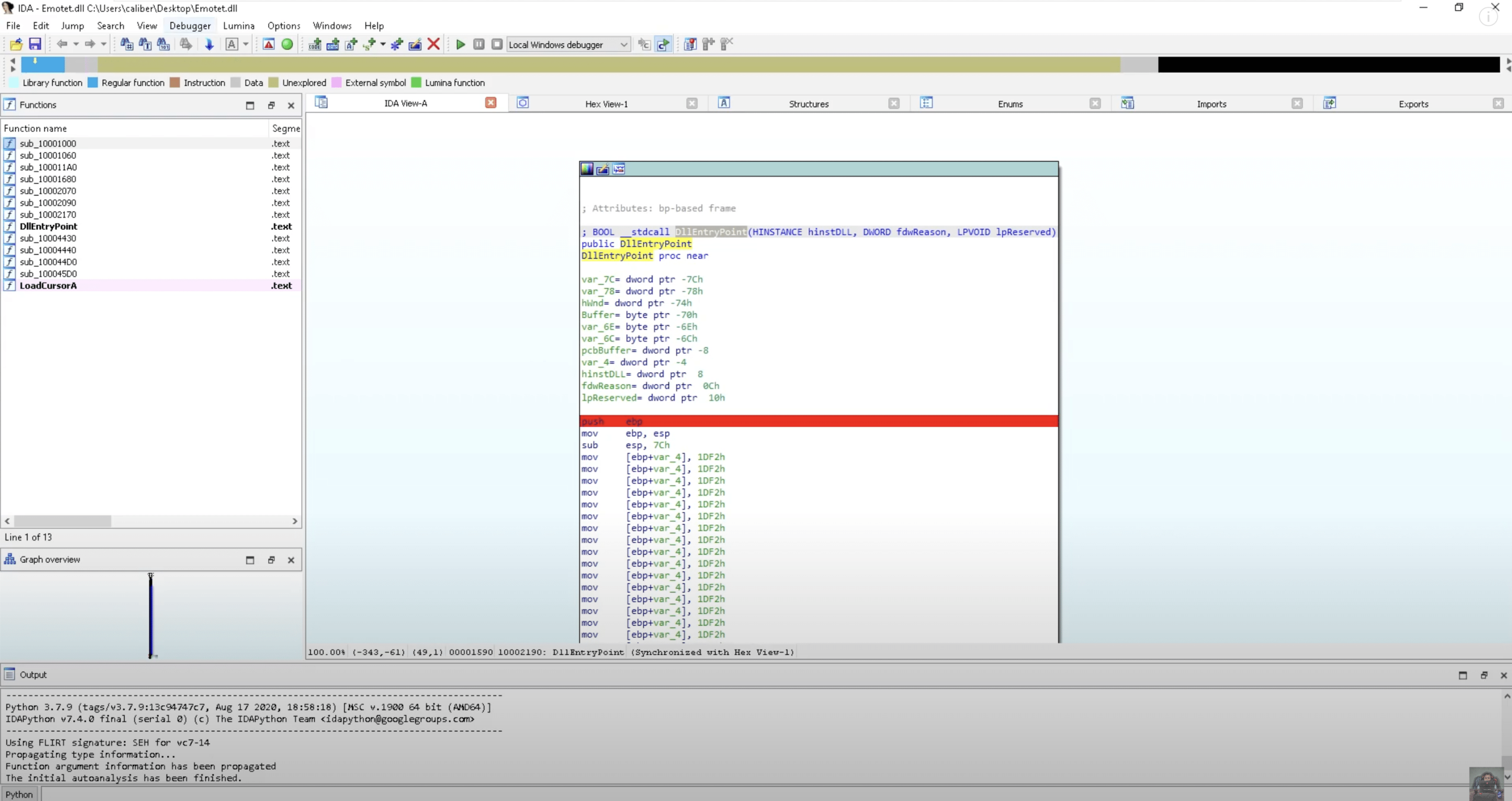
People who are drawn to malware analysis are usually not satisfied with surface-level answers. They want to understand what is actually happening, why it is happening, and what sits beneath the behavior they are seeing. That matters in this field, because much of the work involves making sense of things that are hidden, layered, or intentionally designed to be hard to understand.
You do not give up when the answer takes time
Malware analysis is not a field for people who need instant clarity. A lot of the work involves sitting with uncertainty, following a problem longer than feels comfortable, and staying engaged even when progress is slow. The people who grow into this path are often not just intelligent, but persistent. They are willing to keep digging until the picture becomes clearer, even when the answer does not reveal itself quickly.
You are comfortable looking at problems from more than one angle
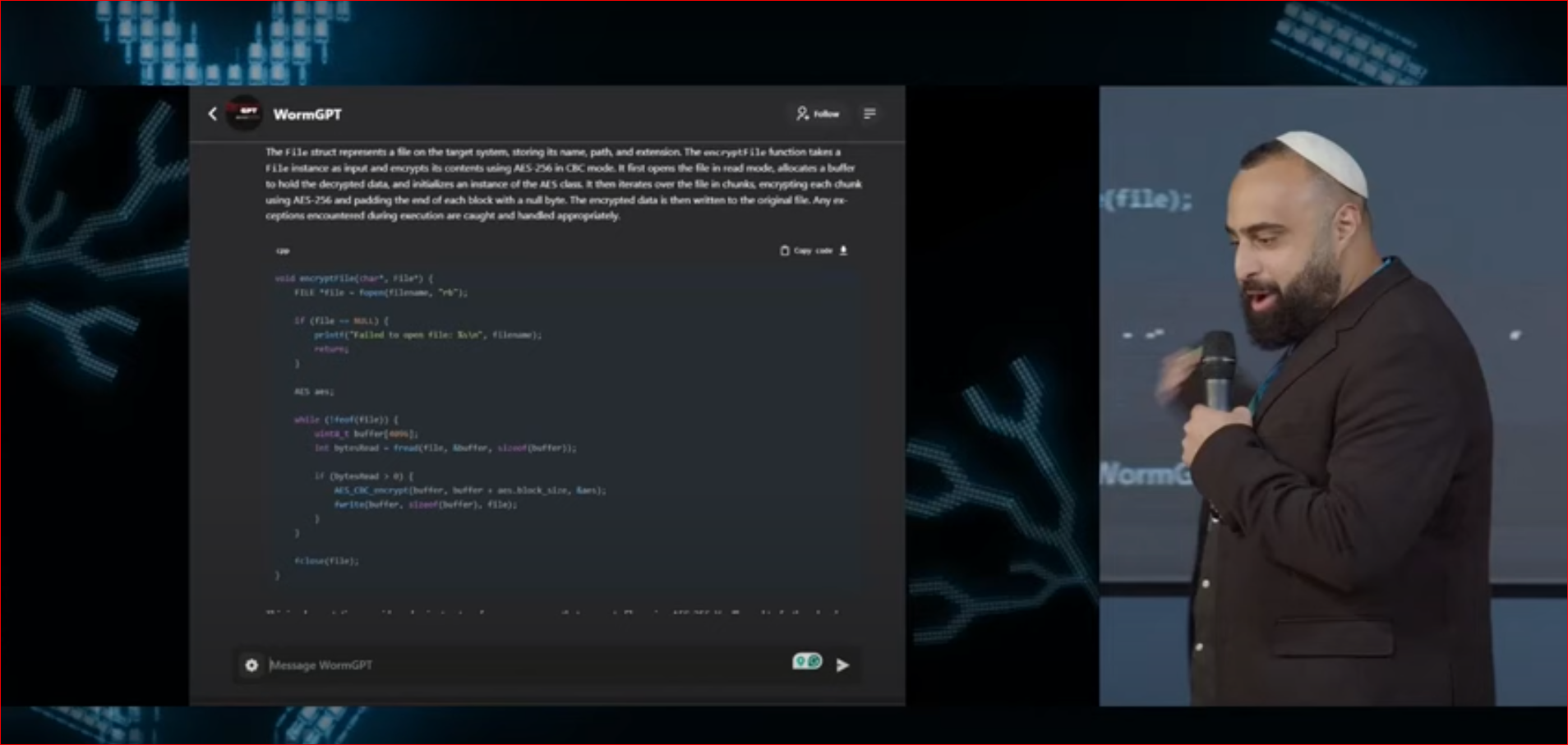
Malware analysis is often seen as a defensive role, but in practice it requires more than defensive thinking alone. To understand malicious code well, you also have to think like the person who built it. That means shifting perspective: not just asking how to stop a threat, but also how it works, why it behaves the way it does, and what the attacker was trying to achieve. For the right person, that mix of defensive thinking and attacker mindset is part of what makes the field so interesting.
This Path Takes More Than Interest Alone
Malware analysis takes more than curiosity or first impressions. To grow in this field, you need real drive – the kind that keeps you learning even when progress is slow, technical, and sometimes frustrating. People who do well here are usually the ones who stay committed to the process, keep sharpening their skills, and are willing to invest in depth over time. That kind of motivation matters, because this is not a path where quick interest is enough on its own.
What Background Do You Need Before This Path Becomes Realistic?
Malware analysis becomes much more realistic once you have a strong foundation in operating systems, networking, and core security concepts. You need to understand how systems normally behave before you can recognize what makes malicious behavior different. Just as important, you need some understanding of how attacks work in practice and how defenders investigate them. This is one of the reasons malware analysis is rarely a true entry-level role: without that baseline, the more advanced parts of the field are much harder to make sense of.
For readers who want to build that progression in a structured way, SOC Analyst Professional – Foundations is the natural place to begin, and Malware Analyst Professional – Level 1 becomes much more relevant once that baseline is already in place.
Who Is This Path Probably Not Right For?
Malware analysis is not the right fit for everyone, and that is completely fine. In many cases, it is a weaker match for people who:
- want answers quickly and lose patience when things stay unclear
- prefer faster progress over slow, technical problem-solving
- are not naturally drawn to depth or detail
- lose interest when the work becomes repetitive, frustrating, or mentally demanding
If you are looking for a path that feels more immediate, less demanding, or easier to break into quickly, there are usually other roles in cybersecurity that make more sense as a starting point.
So, Is This a Path Worth Exploring?
If you recognize yourself in the traits described here and are willing to build the right foundation, malware analysis could be a strong long-term fit. It is not the easiest path in cybersecurity, but for the right person, that is exactly what makes it meaningful. And if the next step is understanding how this path actually develops in practice- from fundamentals to more advanced malware research- you can read our full Malware Analyst roadmap here