(CVE-2020-8842)
Introduction
MSI TrueColor utility comes as a pre-installed utility program on MSI gaming laptops that is used widely around the world and can also be freely downloaded from the official MSI website.
An attacker can exploit this vulnerability during the post-exploitation phase to achieve privilege escalation and persistence,
by using the technique of implanting an arbitrary unsigned executable which is executed by a signed service that runs with the NT AUTHORITY\SYSTEM privileges on the victim machine.
Liked the content?
Subscribe to the free TrainSec knowledge library, and get insider access to new content, discounts and additional materials.
The Vulnerability
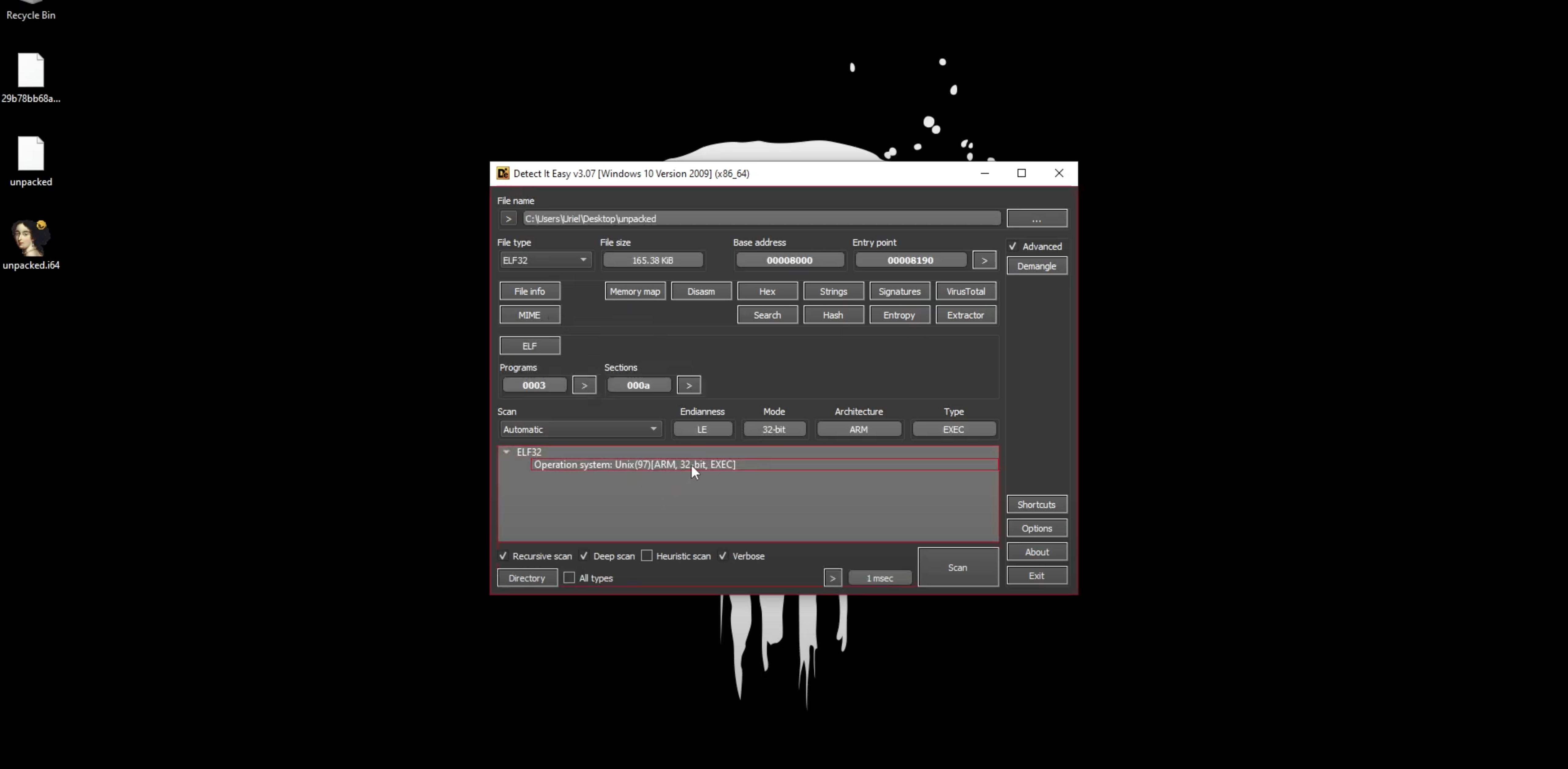
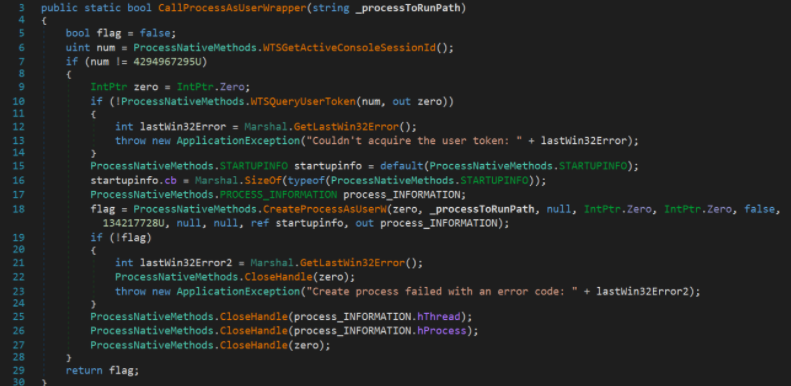
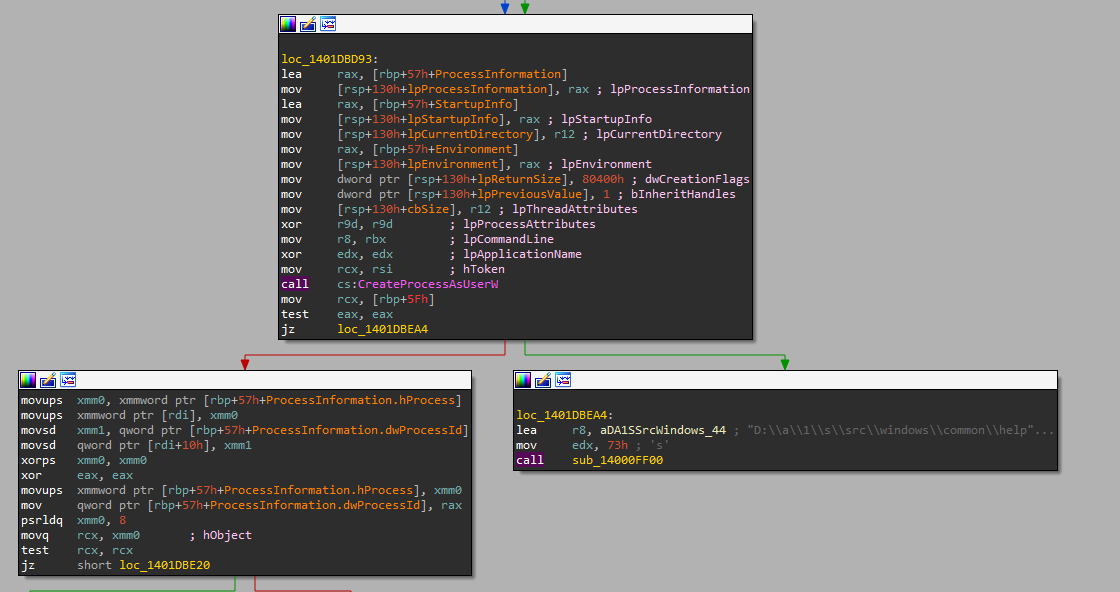
In the Windows operating system, a service is susceptible to “Unquoted Service Path” vulnerability if the executable path is not wrapped with quotation marks. In this case, the Windows service dubbed as “MSITrueColorService” is executed with the “CreateProcessAsUserA” Windows API function as can be seen below:
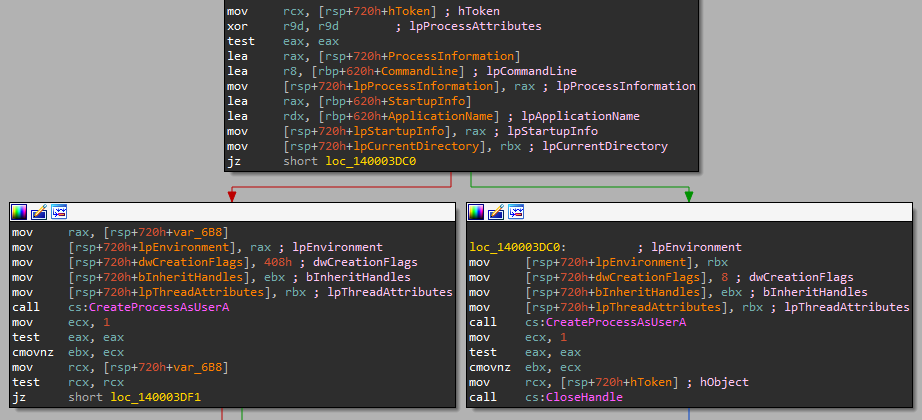
The “CreateProcessAsUserA” Windows API function receives several parameters such as the “lpApplicationName” parameter that has a value of the module/file name or the full path to the module/file, and in this case, with no quotation marks which leads to this vulnerability.
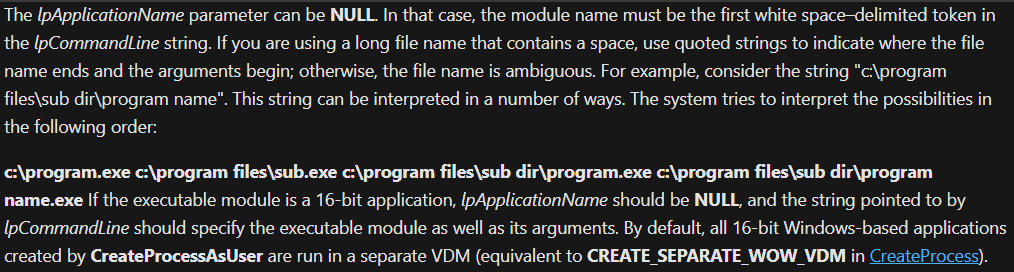
To exploit such vulnerability, an attacker needs to drop a file that will be executed after a computer or service is restarted, either through an administrative account or by abusing a service path followed by insufficient permissions so that any weak user with a “W” (write) permission, for instance, can write to this path without the need of an administrative account. Below you can see Microsoft’s explanation of the “lpApplicationName” parameter:
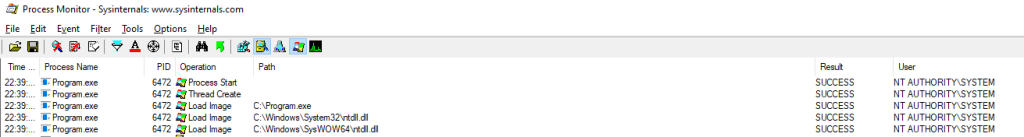
And here below you can see that when the “MSITrueColorService” is executed, it runs as NT AUTHORITY\SYSTEM:
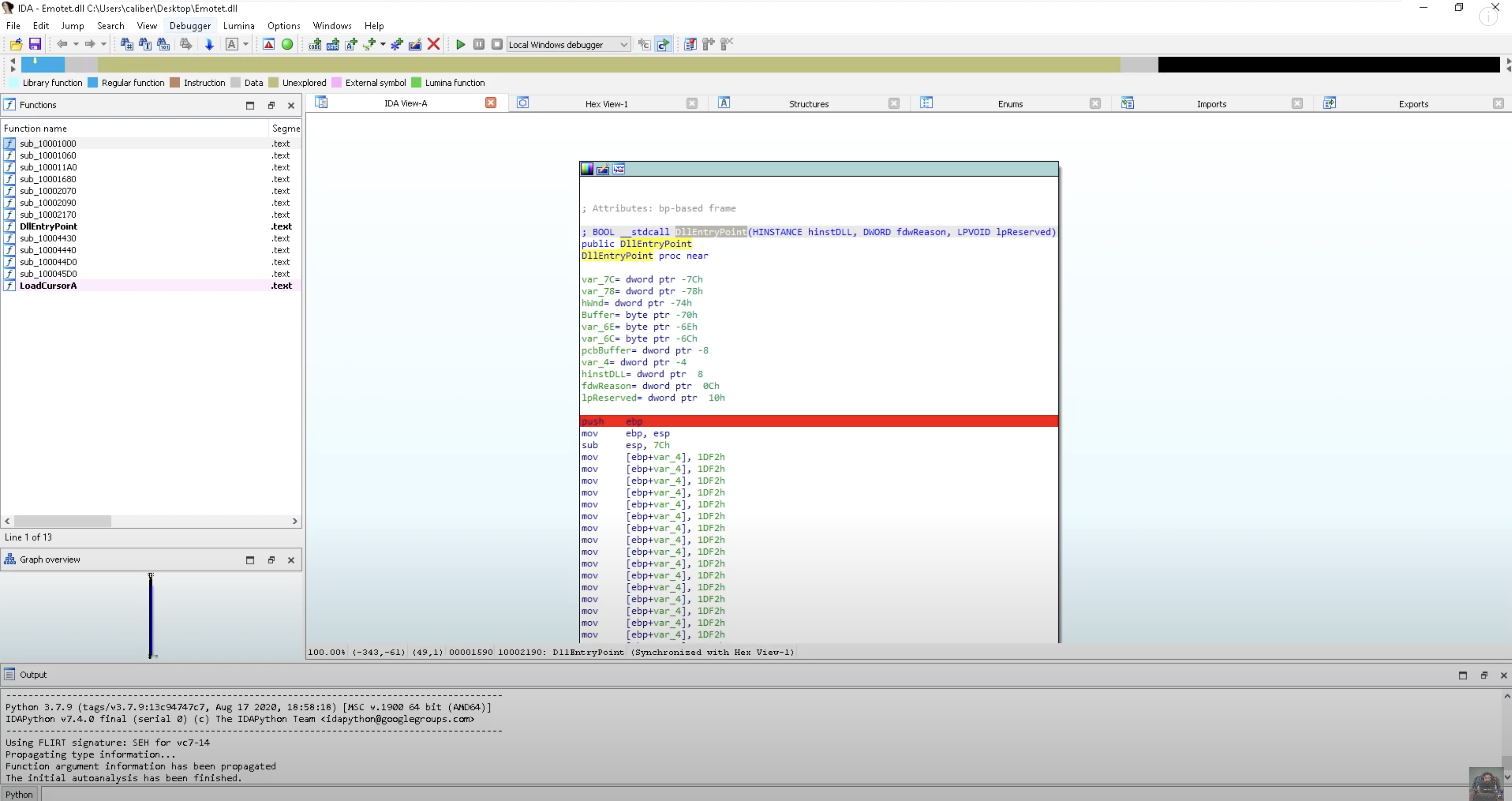
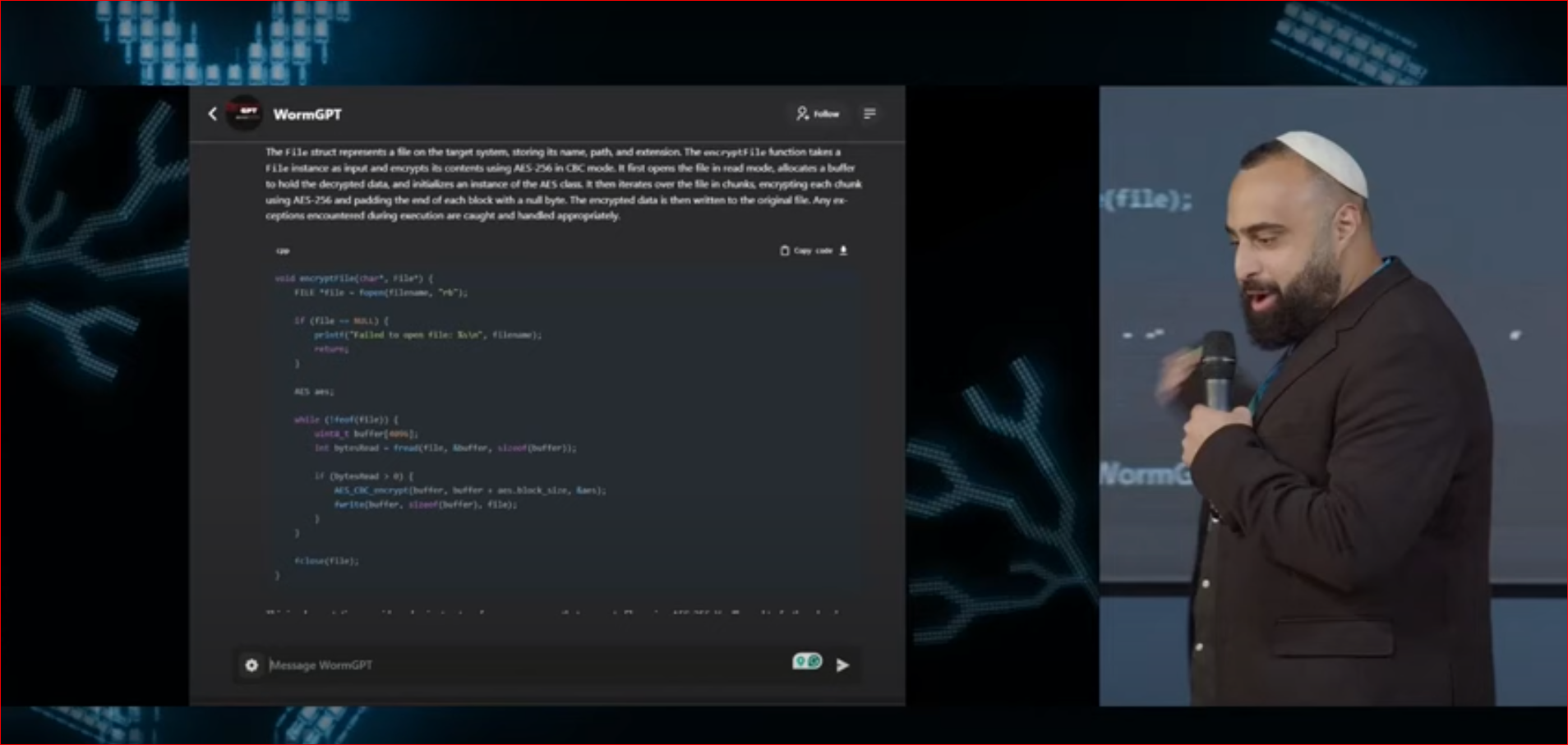
Just to note, such techniques can and are implemented in different kinds of malware. By using malware analysis, we can analyze and dissect malware with such techniques and of course, such techniques are implemented as part of malware development processes by attackers and red teamers alike.
Proof of Concept
The following proof of concept video demonstrates the vulnerability and the exploitation process:
Disclosure Timeline
Feb 10th, 2020 – Vulnerability reported to MITRE
Mar 2nd, 2020 – Initial response from MSI Headquarters.
Mar 20th, 2020 – Issued CVE-2020-8842