If a service doesn’t show up in Services.msc, it’s easy to assume it isn’t installed or it isn’t running. But there’s a third possibility: you’re not allowed to see it.
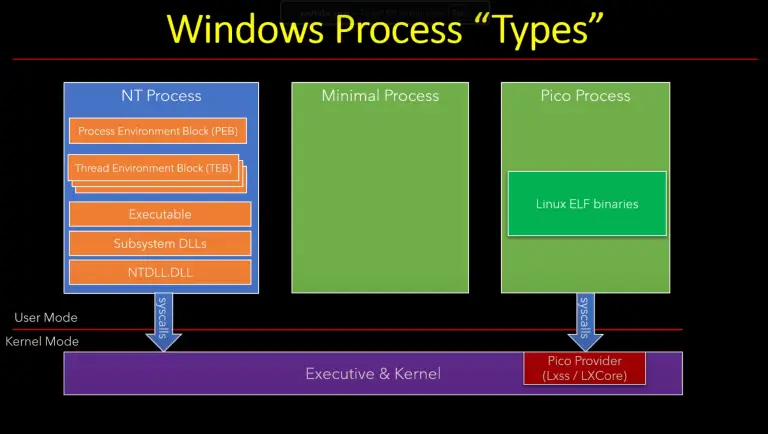
In this post I’m looking at a simple Windows detail: a service can be running normally and still “disappear” from standard service enumeration. Nothing magical is happening. It’s just security. If a caller can’t query a service, the Service Control Manager (SCM) won’t show it to that caller.
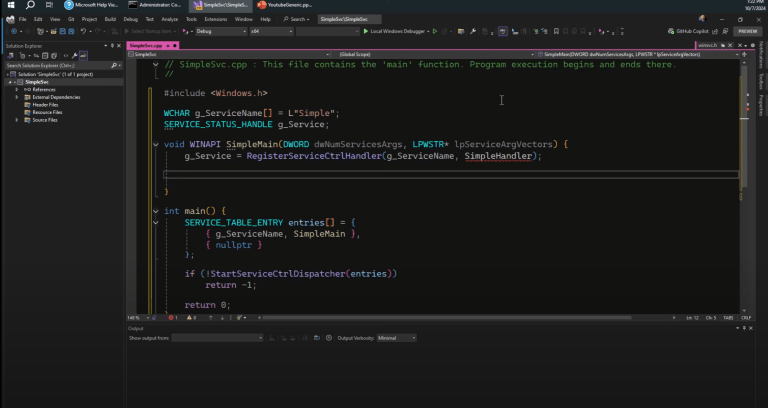
Where Services Are Registered
Service configuration is stored in the system Registry under:
HKLM\SYSTEM\CurrentControlSet\Services
That key contains both services and device drivers (you can distinguish them using the Type value). Because services are registry-backed, many people assume that service visibility is purely a registry permission problem. That assumption is only sometimes true.
Why Services.msc and sc.exe Can Miss A Service
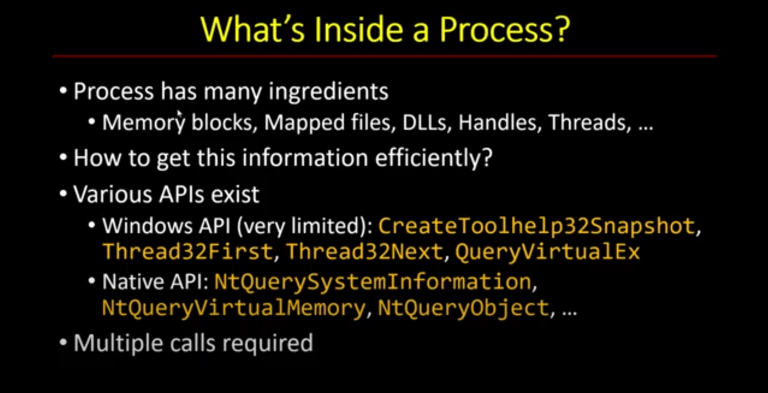
Services.msc (running inside MMC) uses the service control APIs to enumerate services. The same is true for sc.exe when you run commands like sc query.
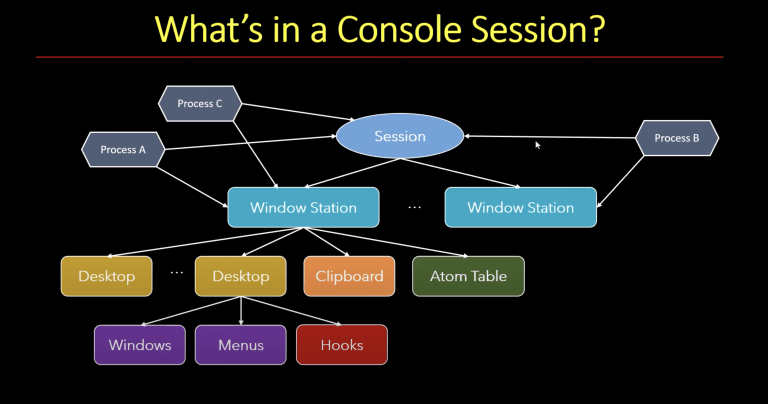
Those APIs talk to the SCM’s internal database. They are not simply walking the Services registry key. And most importantly, enumeration is gated by access checks.
If the SCM can’t open a service with the access required for “read/query,” that service can drop out of the list for that caller. The service can still be running; you just won’t see it through the normal enumeration path.
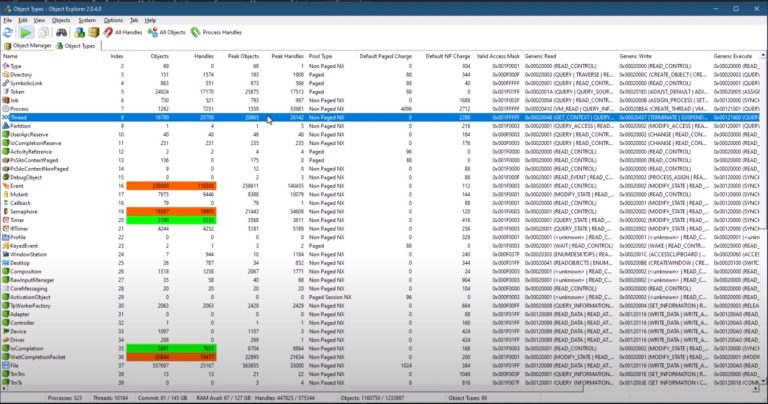
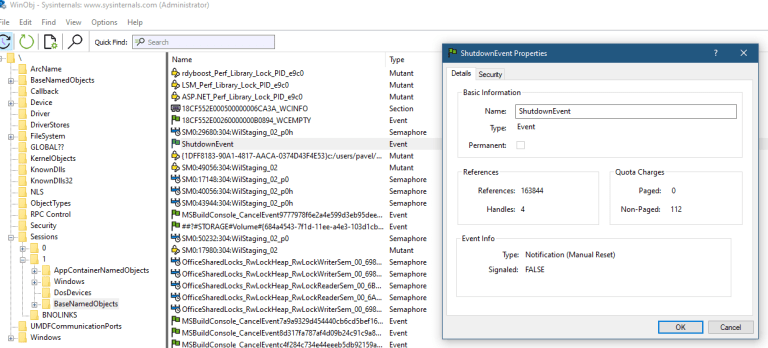
Service Objects Have Security Descriptors
A Windows service is an object managed by the SCM, and it has a security descriptor (with a DACL) that controls who can query it and manage it.
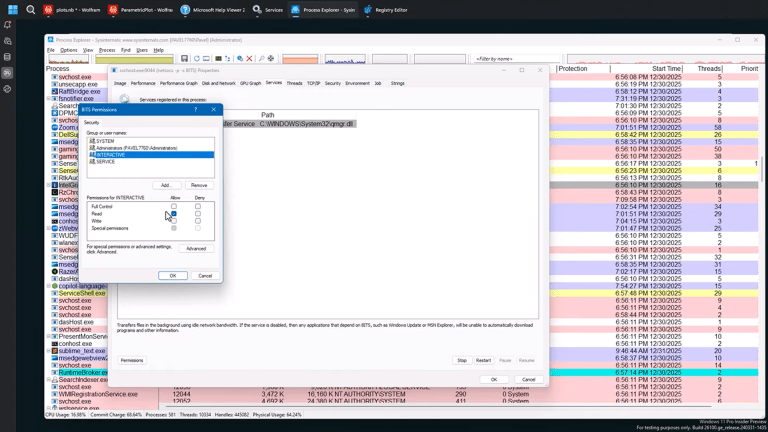
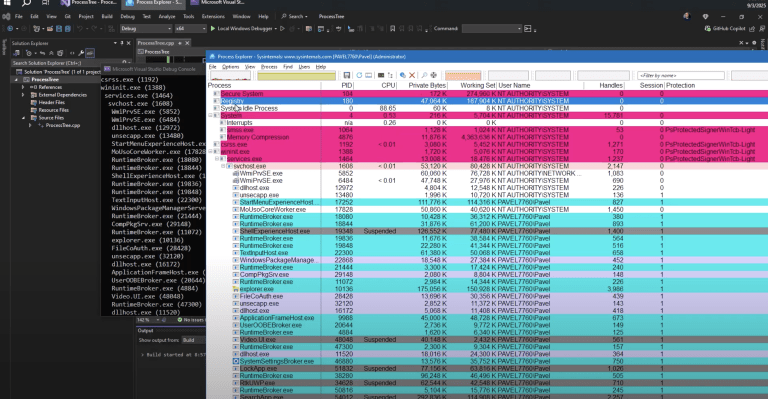
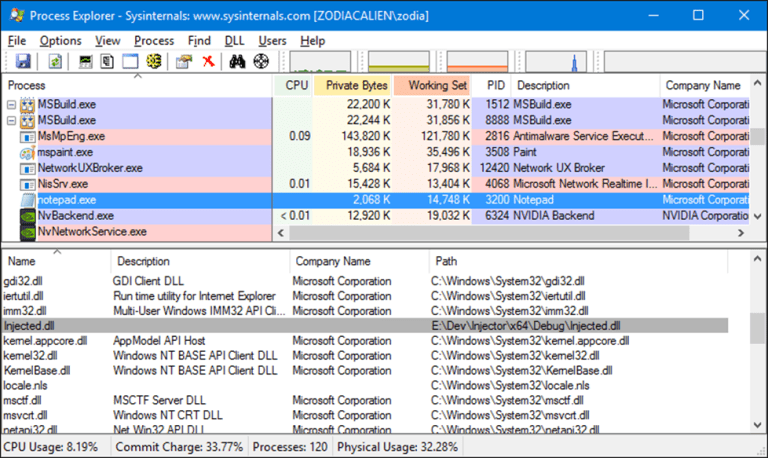
If the relevant query/read permissions are denied for your security context, standard enumeration won’t show the service. In the video I use Process Explorer as a convenient way to view and edit a service’s permissions. The important concept is the DACL, not the tool.
How To Prove The Service Is Still Running
One reason this technique is confusing is that “hidden” does not mean “stopped.”
If you suspect a service is present but not visible through the usual UI, try to confirm it from a different angle:
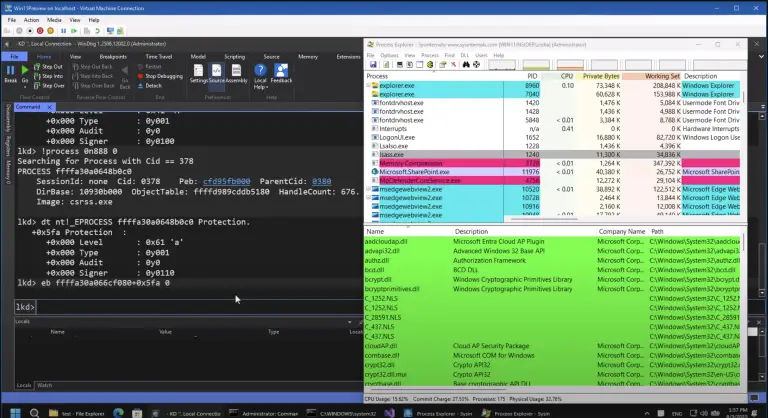
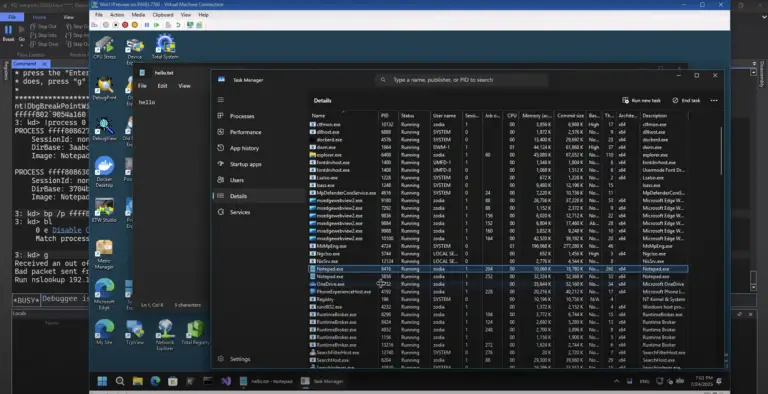
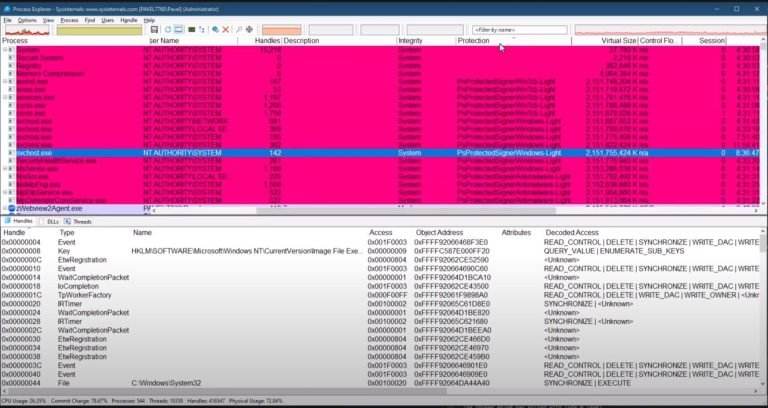
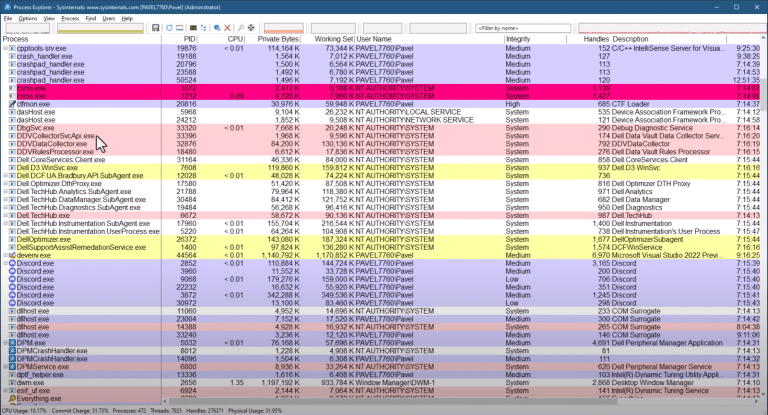
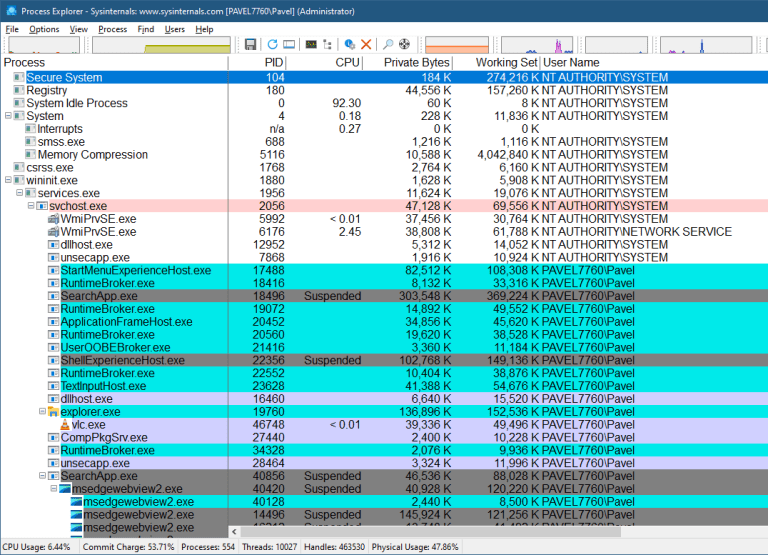
- Task Manager can show you services and the PID hosting them. If the service is hosted inside an svchost instance, you can jump from the service name to the process that’s running it.
- In Process Explorer, a process that hosts services (like the very common svchost) can list the services it hosts. That’s a useful cross-check when a service isn’t appearing where you expect.
The point is not that these tools are “better.” The point is that they’re giving you different views of the same system.

$2,111
$1,478 or $150 X 10 payments
Windows Master Developer
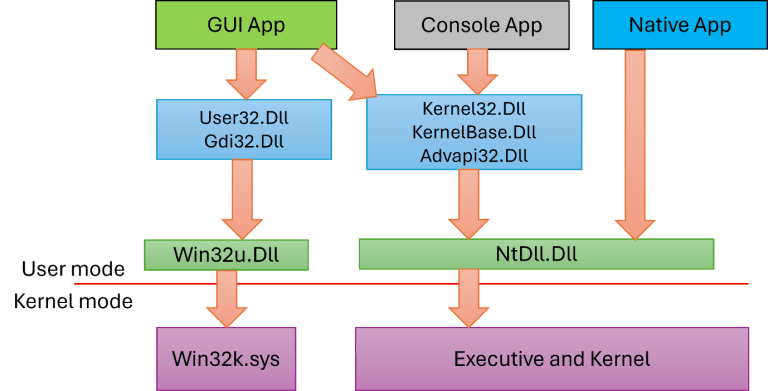
Takes you from a “generic” C programmer to a master Windows programmer in user mode and kernel mode.
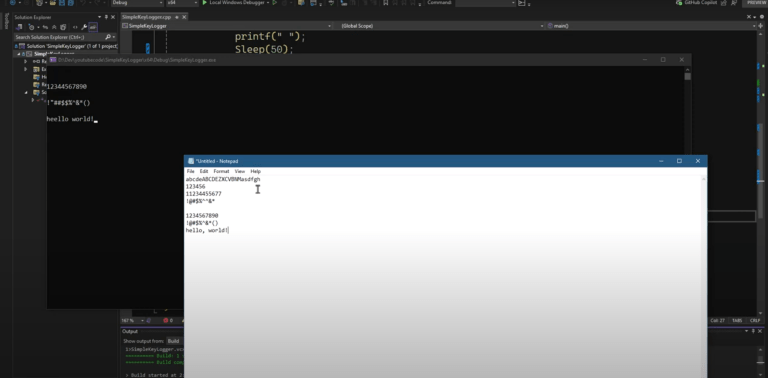
What “Hidden” Looks Like In Practice
When service permissions block enumeration, you typically see:
- In Services.msc, the service is not listed (even if it is running).
- In
sc query, the service doesn’t show up in the full list. - If you already know the exact service name and query it directly, you get Access Denied (not “not found”).
That last point matters. “Not found” means the SCM can’t locate it. “Access denied” means the SCM found it, but you’re not allowed to query it.
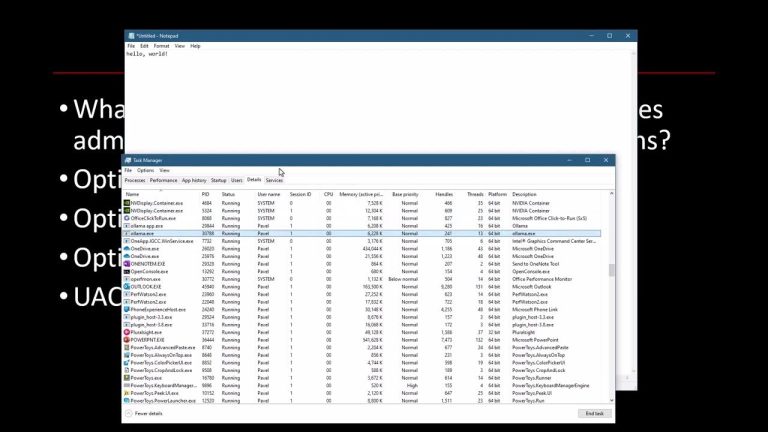
Why “Admin” Visibility Is Not Guaranteed
A detail that surprises people is that this can happen even when you run the management tool “as administrator.”
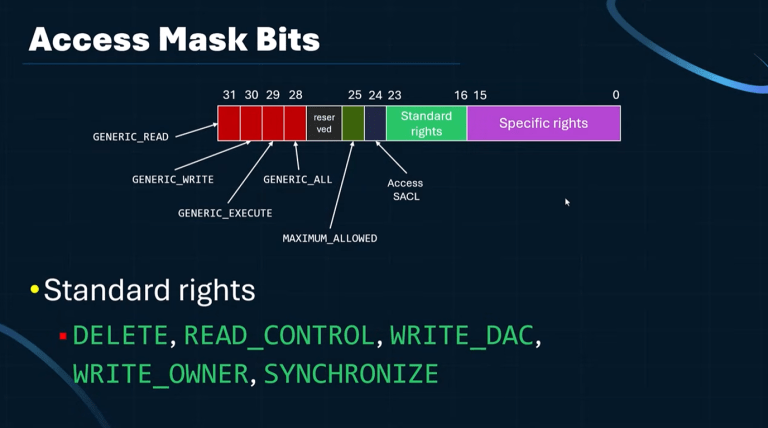
Being elevated does not automatically mean you can query every service. The SCM evaluates the service’s DACL against your token, and explicit deny entries take precedence over allow entries. Windows even warns about this: deny ACEs are evaluated before allow ACEs.
There’s also a practical escape hatch: ownership. The owner of an object is in a privileged position and can recover access by changing the DACL. That’s why these changes are reversible if you still have sufficient rights.
Why Some Tools Still Find The Service
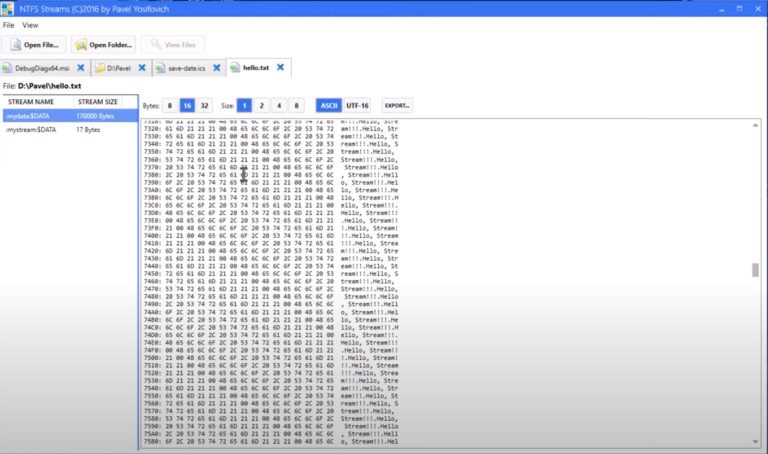
Not every tool discovers services through the SCM APIs. Autoruns is a good example: it can enumerate services by reading the registry directly.
So a service that disappears from Services.msc can still appear in Autoruns, because Autoruns is looking at HKLM\SYSTEM\CurrentControlSet\Services rather than relying on SCM enumeration.
This is the defensive lesson: don’t trust a single enumeration path.
$1,938
$1,356 or $140 X 10 payments
Windows Internals Master
Broadens and deepens your understanding of the inner workings of Windows.
Defensive Checks That Actually Help
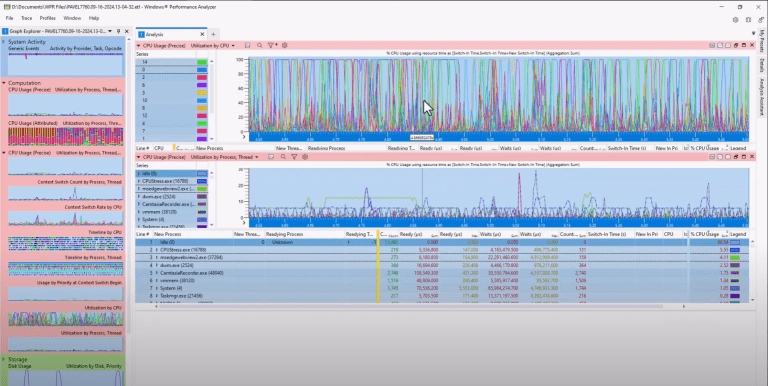
Compare SCM Enumeration With Registry Enumeration
Enumerate services via the SCM APIs (Services.msc, sc.exe, PowerShell), and separately enumerate the Services registry key. A service present in the registry but missing from SCM results is a strong signal that permissions (or corruption) are involved.
Inspect The Service DACL
Look for nonstandard DACLs, especially explicit deny entries against principals that normally have query access. Comparing against a known-good baseline for similar services on the same OS build is usually faster than guessing.
Use Error Semantics As A Clue
Pay attention to the difference between:
- “service does not exist”
- “access is denied”
That distinction alone often tells you whether you’re dealing with visibility/permissions versus a missing service.
Why This Matters For TrainSec Students
Windows visibility depends on access checks, and different tools see different slices of the system depending on which APIs they use.
When tools disagree, don’t stop at “it isn’t there.” Ask what path the tool is using (SCM APIs or Registry) and what permissions that path requires.ion cleanly, it’s a short step to building more advanced tooling.
Liked the content?
Subscribe to the free TrainSec knowledge library, and get insider access to new content, discounts and additional materials.
Keep Learning with TrainSec
This content is part of the free TrainSec Knowledge Library, where students can deepen their understanding of Windows internals, malware analysis, and reverse engineering. Subscribe for free and continue learning with us:
https://trainsec.net/library