Cybersecurity is often seen as a high-paying field, and in many cases, that reputation is justified. But there is no single “cyber security salary.” Pay can vary significantly from one role to another depending on experience, technical depth, specialization, and level of responsibility. A SOC Analyst, for example, will not usually earn the same as a Malware Analyst or a Security Researcher, even though all of them work under the broader umbrella of cybersecurity. That is why salary only becomes meaningful when you compare specific roles and experience levels, rather than the field as a whole.
What Actually Affects Cyber Security Salaries?
There is no single formula for salary in cybersecurity, but a few factors tend to shape compensation more than anything else:
- Years of experience
- Technical depth and specialization
- The role itself
- Company size and industry
- Level of responsibility and ownership
- Communication and leadership ability in more advanced positions
To make those differences easier to understand, it helps to look at common cybersecurity roles and the estimated salary ranges typically associated with each one:
SOC Analyst
What does a SOC Analyst do?
A SOC Analyst is one of the most common entry points into cybersecurity. The role focuses on monitoring alerts, reviewing suspicious activity, identifying possible threats, and escalating incidents that require deeper investigation. Because the work is embedded in day-to-day security operations, it gives professionals practical exposure to how attacks, alerts, and response workflows look inside a real organization.
How much does a SOC Analyst earn?
SOC Analyst salaries typically start at around $50K–$80K per year in the first year. With 1–3 years of experience, the typical range rises to around $70K–$105K annually. At 4+ years of experience, the salary range usually broadens to roughly $95K–$135K per year, depending on the company, the level of responsibility, and the scope of the role.
Want to build the right foundation for a role like this? Start with TrainSec’s SOC Analyst Professional – Foundations.
Incident Response Analyst
What does an Incident Response Analyst do?
An Incident Response Analyst steps in when a security incident requires real investigation and action. The role typically involves determining what happened, understanding how the attack unfolded, helping contain the damage, and supporting the recovery process. Compared with a SOC Analyst, the work is less about routine monitoring and more about handling incidents that require speed, judgment, and a structured investigative approach.
How much does an Incident Response Analyst earn?
Incident Response Analyst salaries typically start at around $70K–$95K per year in the first year. With 1–3 years of experience, the typical range rises to around $90K–$120K annually. At 4+ years of experience, salaries often reach approximately $120K–$165K per year, depending on the organization, the complexity of incidents handled, and the level of responsibility within the team.
Security Engineer
What does a Security Engineer do?
A Security Engineer works on the systems and technical controls that help an organization stay secure over time. Depending on the company, the role may include hardening environments, improving detection and prevention capabilities, supporting secure architecture, and helping close security gaps before they are exploited. Compared with more operational roles, it usually involves greater ownership and deeper technical responsibility.
How much does a Security Engineer earn?
Security Engineer salaries typically start at around $80K–$115K per year in the first year. With 1–3 years of experience, the typical range rises to around $100K–$140K annually. At 4+ years of experience, salaries often reach approximately $135K–$190K per year, depending on the organization, the technical scope of the role, and the level of responsibility involved.
Penetration Tester
What does a Penetration Tester do?
A Penetration Tester looks for security weaknesses before a real attacker can exploit them. The role typically involves testing systems, applications, and environments for exploitable gaps, demonstrating how those weaknesses could be abused, and helping organizations understand where they are most exposed. Compared with roles such as SOC or Incident Response, this work is generally more proactive and attacker-focused by nature.
How much does a Penetration Tester earn?
Penetration Tester salaries typically start at around $70K–$105K per year in the first year. With 1–3 years of experience, the typical range rises to around $95K–$135K annually. At 4+ years of experience, salaries often reach approximately $135K–$175K per year, depending on the company, the technical scope of the work, and the level of responsibility involved.
Malware Analyst
What does a Malware Analyst do?
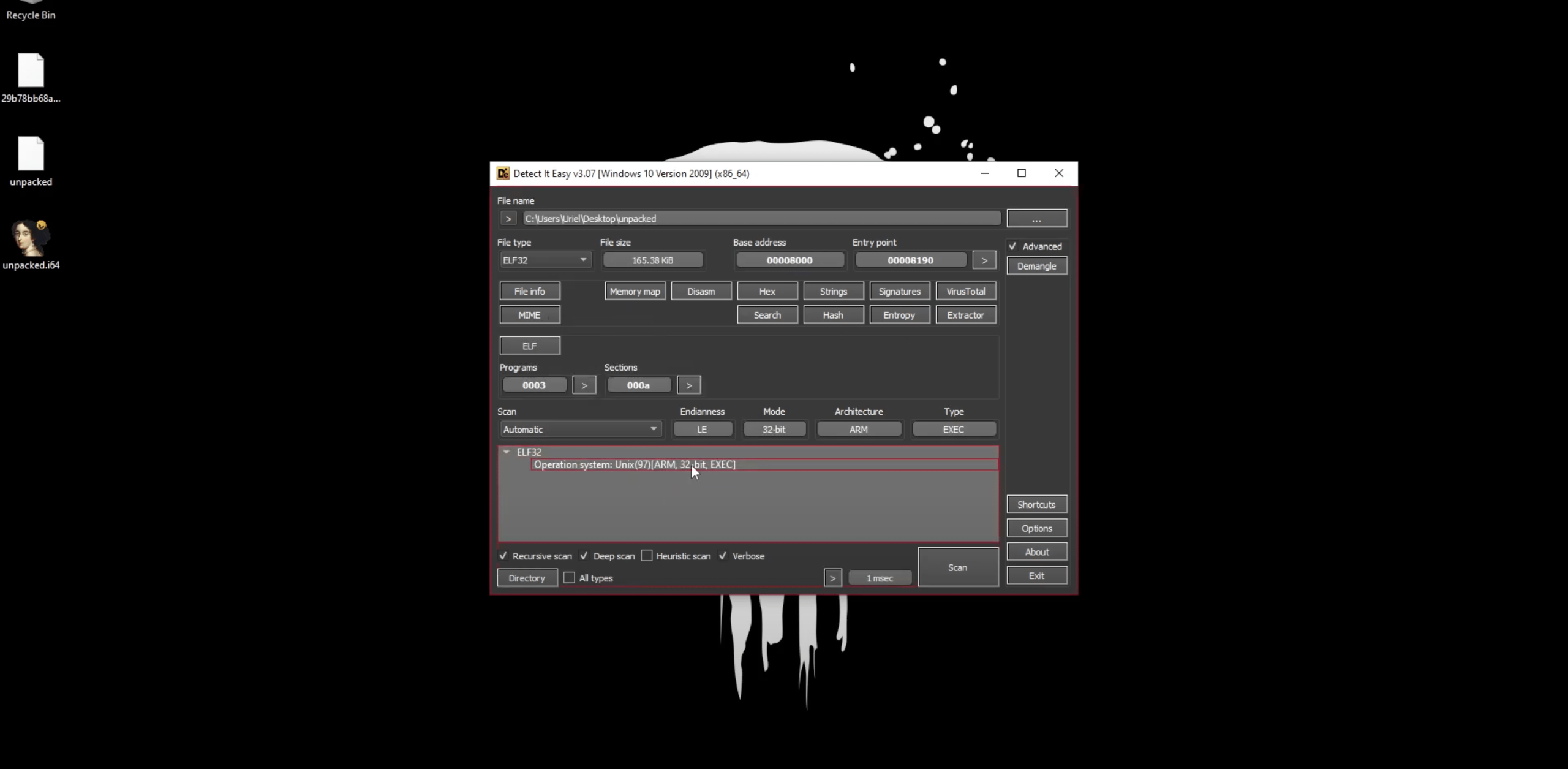
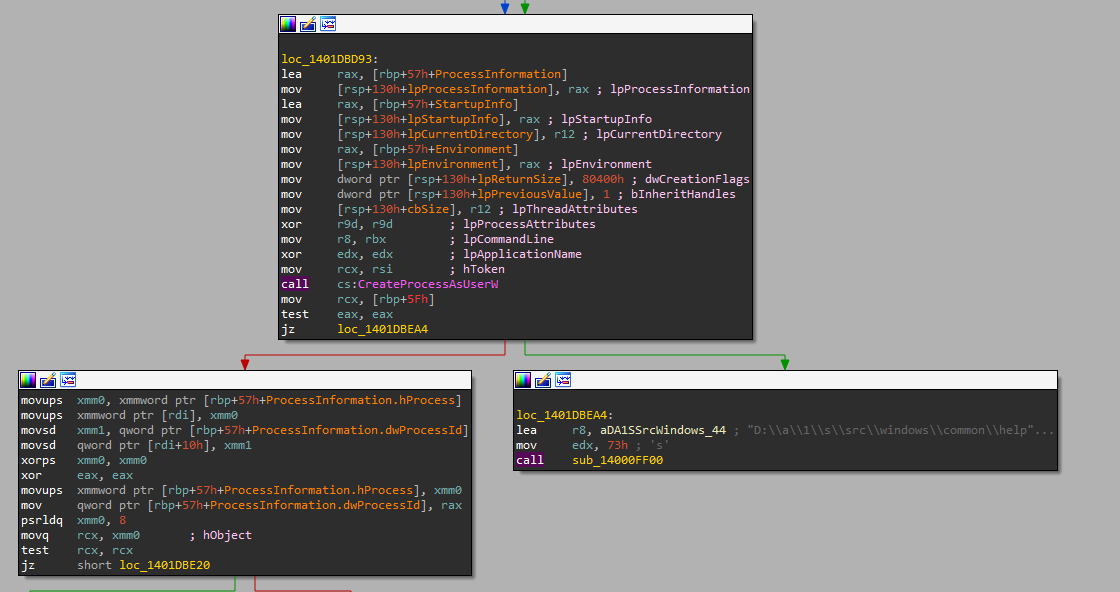
A Malware Analyst investigates malicious code to understand what it does, how it works, and what kind of threat it creates. In practice, the role may involve analyzing suspicious files or scripts, examining behavior, identifying attacker techniques, and turning those findings into reports, detections, or defensive recommendations. Compared with broader cybersecurity roles, this is a more specialized path that usually requires stronger technical foundations.
How much does a Malware Analyst earn?
Malware Analyst salaries typically start at around $70K–$95K per year in the first year. With 1–3 years of experience, the typical range rises to around $90K–$130K annually. At 4+ years of experience, salaries often reach approximately $115K–$170K per year. Because this is a more specialized role with fewer widely available salary benchmarks than some other cyber security positions, these figures should be viewed as broad market estimates rather than an exact range.
If you want to understand how this path usually develops over time, start with our complete Malware Analyst roadmap. And when you are ready to go deeper, TrainSec offers dedicated training through Malware Analyst Professional – Level 1 and Level 2.
Security Researcher
What does a Security Researcher do?
A Security Researcher works at the deeper end of cybersecurity, where the focus is on understanding threats at a much more technical level. Depending on the role, that can include studying new attack techniques, analyzing vulnerabilities, improving detections, investigating malicious behavior, and producing insights that help security teams stay ahead of emerging threats. Compared with more operational positions, this path is typically more specialized and research-heavy.
How much does a Security Researcher earn?
Security Researcher salaries typically start at around $85K–$110K per year in the first year. With 1–3 years of experience, the typical range rises to around $100K–$140K annually. At 4+ years of experience, salaries often reach approximately $145K–$200K per year, depending on the company, the research focus, and the level of technical depth and responsibility involved.
If you are interested in more research-focused roles, TrainSec also offers advanced courses like Windows Security Researcher and EDR Internals – Research & Development.
To make the comparison easier, here is a simplified view of the salary ranges across the main roles covered in this guide:
| Role | Typical Path Level | 0-1 years | 1-3 years | 4+ years |
|---|---|---|---|---|
| SOC Analyst | Entry-level | $50K–$80K | $70K–$105K | $95K–$135K |
| Incident Response Analyst | Mid-level | $70K–$95K | $90K–$120K | $120K–$165K |
| Security Engineer | Mid-level | $80K–$115K | $100K–$140K | $135K–$190K |
| Penetration Tester | Mid-to-Advanced | $70K–$105K | $95K–$135K | $135K–$175K |
| Malware Analyst | Advanced | $70K–$95K | $90K–$130K | $115K–$170K |
| Security Researcher | Advanced | $85K–$110K | $100K–$140K | $145K–$200K |
The salary figures in this table are estimated annual ranges based on publicly available market data from sources such as Glassdoor, SalaryExpert, and PayScale. They reflect general compensation patterns by experience level and may vary depending on location, company type, specialization, and level of responsibility.
Cybersecurity can be a highly rewarding field, but salary alone is not a good reason to choose a path. As the roles in this guide show, higher pay often comes with deeper specialization, greater technical responsibility, and a steeper learning curve. That is why it makes more sense to choose a role not only based on compensation, but also on the kind of work it involves and the direction you want your career to take. In the long run, the best path is not simply the one that pays the most, but the one that aligns with your skills, interests, and long-term goals.